A couple of hours ago, Bitrated, a bitcoin trust platform meant for reputation management and consumer protection has posted a tweet, warning users about an ongoing DDoS attack, carried out in the form of an extortion attempts. During the last couple of weeks, numerous Bitcoin-related companies, but also other businesses from all around the world have been affected by such attacks. According to a Medium post written by the Bitrated, it seems like they received a warning mail five minutes prior to the commencement of the attack, asking for a total of 7 BTC, worth around $3,200 at the time of writing. Unlike other extortionists who decided not to stand up to their promise, Bitrated’s servers were attacked for a couple of hours, and were put under a strain of 3.2 Gb/s. In return, DigitalOcean null routed trading on their network infrastructure. According to Bitrated, the company has an ethic code which makes them unable to succumb to any extortion attempts. They believe that blackmail demands are unethical, and funding the extortionists will undoubtedly lead to further attacks. Bitrated also mentioned that due to their nature of being a bootstrapped startup, they do not have the financial resources required to counter-attack such demands, which is why the service may be unavailable for a while. Based on everything that has been outlined so far, what do you personally think about this DDoS attack? Let us know your thoughts in the comment section below. UPDATE: The DDoS attacks have stopped. Therefore, the platform is available. Bitrated encourages users who wish to do so, to withdraw their funds from the system as soon as possible. Source: http://themerkle.com/bitrated-faces-severe-ddos-attack-and-3200-ransom-demand/
Read the article:
Bitrated faces severe DDoS attack and $3,200 ransom demand

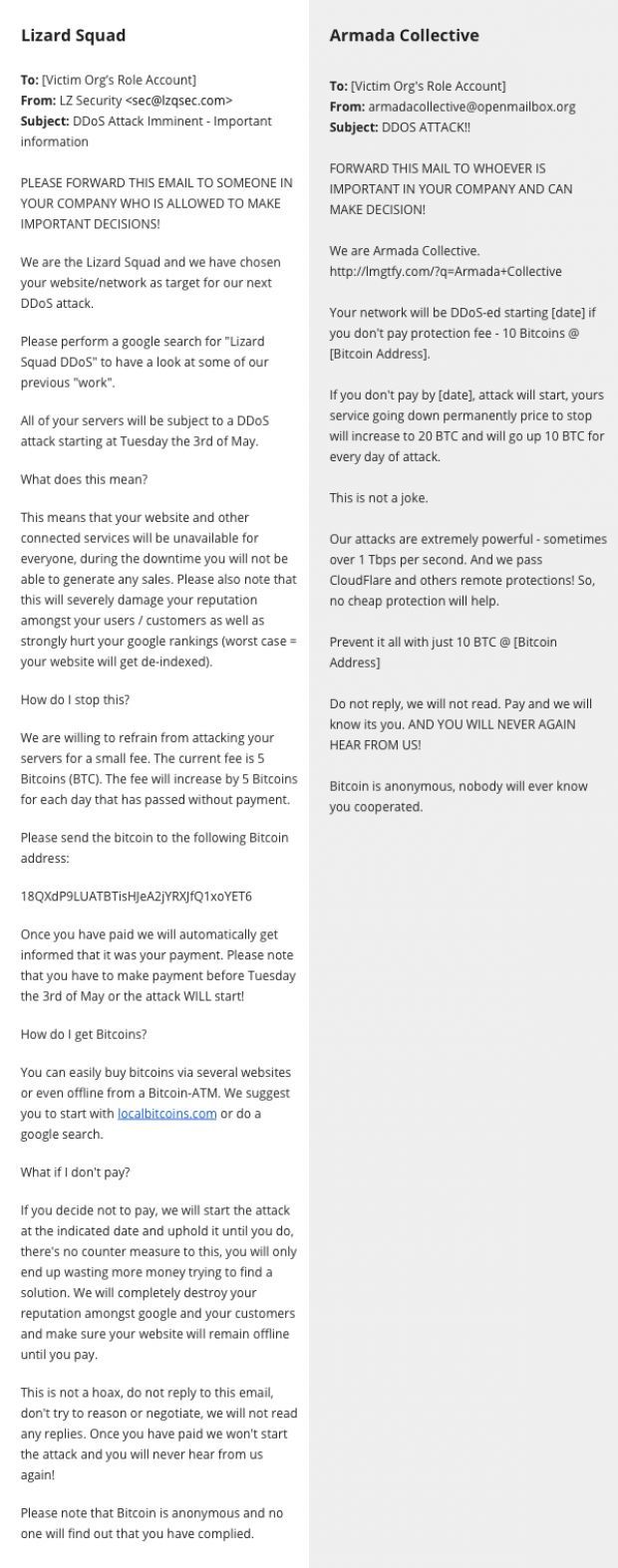
 After terrorizing companies under the fake Armada Collective moniker, the same group appears to have switched to using the name of the infamous Lizard Squad hacking crew, CloudFlare reported today. Early this week on Monday, CloudFlare let everyone know there was a criminal goup sending out extortion emails to companies around the globe. The criminals were posing as Armada Collective , an infamous group known for carrying out DDoS attacks if victims didn’t pay a so-called “protection tax.” The crooks were basing their attacks on the victims googling their name and finding out about the tactics of the real Armada Collective. In fact, CloudFlare says it never saw a single DDoS attack carried out by this group against its targets. In another blog post today, CloudFlare says that three days after they exposed the group, the criminals dropped the Armada Collective name and started using Lizard Squad instead, another hacking crew, famous for downing the Xbox and PlayStation networks on Christmas 2014. The change was to be expected since extorted organizations that would google the Armada Collective name would see all the stories about the copycats instead. CloudFlare says that over 500 companies received extortion emails from this group claiming to be Lizard Squad and that all these emails were identical. As before, the group used one single Bitcoin address to receive payments. By using one Bitcoin address, the group would not be able to tell which companies paid the ransom and which didn’t, meaning this was almost sure the same group as before, launching empty threats once again. CloudFlare says that just like when claiming to be Armada Collective, the group never launched any DDoS attacks when posing as Lizard Squad. Below is a comparison of the two ransom notes received by companies, from the fake Lizard Squad group on the left, and from the fake Armada Collective group on the right. Source: http://justfreedownload.net/news/98693/armada-collective-copycats-now-posing-as-lizard-squad-in-ddos-extortion-scheme.html
After terrorizing companies under the fake Armada Collective moniker, the same group appears to have switched to using the name of the infamous Lizard Squad hacking crew, CloudFlare reported today. Early this week on Monday, CloudFlare let everyone know there was a criminal goup sending out extortion emails to companies around the globe. The criminals were posing as Armada Collective , an infamous group known for carrying out DDoS attacks if victims didn’t pay a so-called “protection tax.” The crooks were basing their attacks on the victims googling their name and finding out about the tactics of the real Armada Collective. In fact, CloudFlare says it never saw a single DDoS attack carried out by this group against its targets. In another blog post today, CloudFlare says that three days after they exposed the group, the criminals dropped the Armada Collective name and started using Lizard Squad instead, another hacking crew, famous for downing the Xbox and PlayStation networks on Christmas 2014. The change was to be expected since extorted organizations that would google the Armada Collective name would see all the stories about the copycats instead. CloudFlare says that over 500 companies received extortion emails from this group claiming to be Lizard Squad and that all these emails were identical. As before, the group used one single Bitcoin address to receive payments. By using one Bitcoin address, the group would not be able to tell which companies paid the ransom and which didn’t, meaning this was almost sure the same group as before, launching empty threats once again. CloudFlare says that just like when claiming to be Armada Collective, the group never launched any DDoS attacks when posing as Lizard Squad. Below is a comparison of the two ransom notes received by companies, from the fake Lizard Squad group on the left, and from the fake Armada Collective group on the right. Source: http://justfreedownload.net/news/98693/armada-collective-copycats-now-posing-as-lizard-squad-in-ddos-extortion-scheme.html 
 In less than two months, online businesses have paid more than $100,000 to scammers who set up a fake distributed denial-of-service gang that has yet to launch a single attack. The charlatans sent businesses around the globe extortion e-mails threatening debilitating DDoS attacks unless the recipients paid as much as $23,000 by Bitcoin in protection money, according to a blog post published Monday by CloudFlare, a service that helps protect businesses from such attacks. Stealing the name of an established gang that was well known for waging such extortion rackets, the scammers called themselves the Armada Collective. “If you don’t pay by [date], attack will start, yours service going down permanently price to stop will increase to increase to 20 BTC and will go up 10 BTC for every day of the attack,” the typical demand stated. “This is not a joke.” Except that it was. CloudFlare compared notes with other DDoS mitigation services and none of them could find a single instance of the group acting on its threat. CloudFlare also pointed out that the group asked multiple victims to send precisely the same payment amounts to the same Bitcoin addresses, a lapse that would make it impossible to know which recipients paid the blood money and which ones didn’t. Despite the easily spotted ruse, many businesses appear to have fallen for the scam. According to a security analyst contacted by CloudFlare, Armada Collective Bitcoin addresses have received more than $100,000. “The extortion emails encourage targeted victims to Google for the Armada Collective,” CloudFlare CEO Matthew Prince wrote. “I’m hopeful this article will start appearing near the top of search results and help organizations act more rationally when they receive such a threat.” Source: http://arstechnica.com/security/2016/04/businesses-pay-100000-to-ddos-extortionists-who-never-ddos-anyone/
In less than two months, online businesses have paid more than $100,000 to scammers who set up a fake distributed denial-of-service gang that has yet to launch a single attack. The charlatans sent businesses around the globe extortion e-mails threatening debilitating DDoS attacks unless the recipients paid as much as $23,000 by Bitcoin in protection money, according to a blog post published Monday by CloudFlare, a service that helps protect businesses from such attacks. Stealing the name of an established gang that was well known for waging such extortion rackets, the scammers called themselves the Armada Collective. “If you don’t pay by [date], attack will start, yours service going down permanently price to stop will increase to increase to 20 BTC and will go up 10 BTC for every day of the attack,” the typical demand stated. “This is not a joke.” Except that it was. CloudFlare compared notes with other DDoS mitigation services and none of them could find a single instance of the group acting on its threat. CloudFlare also pointed out that the group asked multiple victims to send precisely the same payment amounts to the same Bitcoin addresses, a lapse that would make it impossible to know which recipients paid the blood money and which ones didn’t. Despite the easily spotted ruse, many businesses appear to have fallen for the scam. According to a security analyst contacted by CloudFlare, Armada Collective Bitcoin addresses have received more than $100,000. “The extortion emails encourage targeted victims to Google for the Armada Collective,” CloudFlare CEO Matthew Prince wrote. “I’m hopeful this article will start appearing near the top of search results and help organizations act more rationally when they receive such a threat.” Source: http://arstechnica.com/security/2016/04/businesses-pay-100000-to-ddos-extortionists-who-never-ddos-anyone/