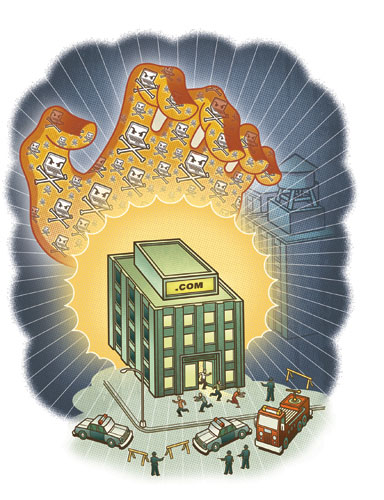
One of the biggest ongoing challenges in networking continues to be the struggle against distributed denial of service (DDoS) attacks. Unlike the similarly-named denial of service (DoS) attack, which is easily controlled by filtering all packets from a particular source IP address, a distributed DOS attack usually includes traffic generated by large numbers of host computers. These hosts may be in multiple geographic regions, and often are served by multiple ISPs.
The intent of these attacks is the same—to overwhelm Internet sites with so many packets that they lose connectivity, disrupting operations and potentially causing large financial losses. Sites under attack may find all their bandwidth consumed, or simply that their firewalls or servers cannot withstand so much traffic. Occasionally attackers will find an actual weakness or vulnerability in the site, but this is not necessary for a DDoS attack to succeed. Every organization with a public Internet site is a potential DDoS victim.
Reasons behind DDoS attacks may include extortion, market competition, political sabotage or even cyber terrorism. The mechanism is usually the same—most attackers use botnets.
Botnets are collections of autonomous software robots or “bots,†running on multiple infected computers (sometimes called “zombiesâ€) without the knowledge or consent of those systems’ owners. Located mostly in Windows PCs, bots wait in hiding until a hacker secretly signals them. Hackers often use Internet relay chat as a way to command botnets, remotely telling them to generate spam, attack a website or infect other computers (and thus add to the size of the botnet and its value to the hacker who controls it).
More than a million bots are estimated to exist on the public Internet, and some botnets consist of more than 20,000 infected PCs. When a botnet of that size targets a single website, even the largest sites with huge servers and prodigious bandwidth may not be able to withstand the attack. According to the Computer Security Institute, corporations such as Amazon, Microsoft, Yahoo, CNN and eBay have been victims of DDoS attacks. And DDoS attacks can be launched against more than just host computers or Web servers—they have been directed at DNS servers, email systems and network routers.
Read More..

 The Host Guru are running an interview with Derek Raines of Gigenet which is well known for the DDoS attack filtering they offer their customers. Derek talks about the industry they are in, the types of customers they service, the attacks they have thwarted and whether or not fears of internet terrorism is driving sales.
The Host Guru are running an interview with Derek Raines of Gigenet which is well known for the DDoS attack filtering they offer their customers. Derek talks about the industry they are in, the types of customers they service, the attacks they have thwarted and whether or not fears of internet terrorism is driving sales.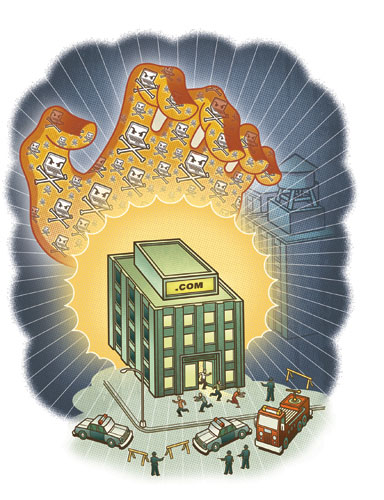

 "EveryDNS, sister company to OpenDNS (which runs the PhishTank anti-phishing initiative), has been hit by a massive distributed denial-of-service attack. The attack started sometime Friday afternoon and, from all indications, was targeting Web sites that used free DNS management services provided by EveryDNS. At the height of the DDoS bombardment, EveryDNS was being hit with more than 400mbps of traffic at each of its four locations around the world. From the article: ‘"We were collateral damage," Ulevitch explained… Because law enforcement is involved, Ulevitch was hesitant to release details of the actual target but there are signs that some of the targets were "nefarious domains" that have since been terminated.’"
"EveryDNS, sister company to OpenDNS (which runs the PhishTank anti-phishing initiative), has been hit by a massive distributed denial-of-service attack. The attack started sometime Friday afternoon and, from all indications, was targeting Web sites that used free DNS management services provided by EveryDNS. At the height of the DDoS bombardment, EveryDNS was being hit with more than 400mbps of traffic at each of its four locations around the world. From the article: ‘"We were collateral damage," Ulevitch explained… Because law enforcement is involved, Ulevitch was hesitant to release details of the actual target but there are signs that some of the targets were "nefarious domains" that have since been terminated.’"