By next spring, researchers are expected to unveil new tools enabling organizations like the Defense Department a rapid response to distributed denial-of-service attacks. The Pentagon has in mind a three-pronged counterattack against a decades-old form of cyber assault that continues to paralyze government and industry networks, despite its low cost of sometimes $10 a hit. Beginning next spring, military-funded researchers are scheduled to produce new tools that would quickly enable organizations to bounce back from so-called distributed denial-of-service attacks. A recovery rate of at most 10 seconds is the goal, according to the Defense Department. Today, attackers have a relatively easy time aiming bogus traffic at computer servers to knock them offline. One reason is that computer systems often are consolidated, making for a wide target area. Another weakness is the predictable behavior of systems that support Web services. And finally, certain types of DDoS attacks that evince little malicious traffic go undetected. Researchers chosen by the Defense Advanced Research Projects Agency will attempt to deny attackers such openings through a three-year program called Extreme DDoS Defense, according to Pentagon officials. The tentative start date is April 1, 2016. The stability of agency operations, banking, online gaming and many other daily activities are at stake here. A DDoS attack against Estonia in 2007 allegedly orchestrated by Russian-backed hackers downed government and industry Internet access nationwide for two weeks. More recently, crooks have begun offering Luddites DDoS-for-hire services at subscription rates of $10-$300 a month, according to journalist Brian Krebs. Lizard Squad, a major provider, allegedly was behind several persistent attacks on online gaming services Xbox and PlayStation. A string of 2011 cyber assaults against Wall Street banks, including Capital One and SunTrust Banks, was attributed to Iranian hackers. Just this month, at the annual Black Hat security conference in Las Vegas, Trend Micro researchers said they observed attackers trying to overpower systems in Washington that monitor the physical security ofgas pumps. Luckily, the devices were fake “honeypot” traps. “Responses to DDoS attacks are too slow and manually driven, with diagnosis and formulation of filtering rules often taking hours to formulate and instantiate. In contrast, military communication often demands that disruptions be limited to minutes or less,” DARPA officials said in an Aug. 14 announcement about the new program. The funding level for the project was not disclosed but multiple grants are expected to be awarded. Interested researchers must submit proposals by noon Oct. 13. XD3 will endeavor to thwart DDoS attacks by “dispersing cyber assets” in facilities and on networks, officials said. Currently, the problem is that cloud computing arrangements and other critical infrastructure systems “rely heavily on highly shared, centralized servers and data centers,” they added. The new tools also will try “disguising the characteristics and behaviors of those assets” to complicate the planning of DDoS launches, officials said. The trick with so-called “low-volume” DDoS attacks is they do not look like traffic overloads. The external computer messages seem benign but are actually exhausting a system’s memory or processors. One workaround here might be sharing information among systems that then can “decide collectively whether attacks have occurred, and/or to determine what mitigations might be most effective,” officials said. One group of XD3 researchers will be assigned to inspect the designs for unintended security holes. Anyone wanting to be a reviewer must hold a top-secret clearance, according to the contract rules. “The objective of design reviews is the proactive identification of weaknesses and vulnerabilities that would reduce the effectiveness of DDoS attack detection or mitigation,” officials said. The idea also is to “apprise performers of potential DDoS attack methods or features that they might not have considered.” Source: http://www.defenseone.com/ideas/2015/08/pentagon-wants-wage-war-denial-service-cyber-attacks/119196/
Read More:
The Pentagon Wants To Wage War on DDoS Cyber Attacks

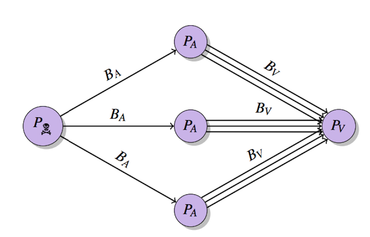
 The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic. A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale. At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks. Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system. In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit. During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request. This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power. City University London DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target. In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet. The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said: “An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim. The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.” In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team. In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times. Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/
The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic. A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale. At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks. Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system. In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit. During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request. This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power. City University London DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target. In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet. The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said: “An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim. The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.” In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team. In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times. Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/