The last week brought confirmation that the Agora online marketplace’s recent downtime has been due to a DDoS attack. It joins the long list of darknet services that have been hit by these recent attacks, which now appear to have mostly been based on the darknet markets being held for ransom by attackers. A string of articles on Deep Dot Web recently revealed the source of the issues. The truth was discovered when a market admin’s account was hacked by TheRealDeal, another marketplace, and the admin’s communication were revealed. It was back at the beginning of May when Mr Nice Guy was hit with DDoS attacks. The offenders demanded 8 bitcoins to be paid within an hour to end the assault; however, the admin had another plan in mind. He wanted to negotiate, and he was willing to pay. He offered the attackers $200 a day or $6000 a month to launch DDoS attacks against rival markets including Agora, Nucleus, BlackBank and AlphaBay. The last week brought confirmation that the Agora online marketplace’s recent downtime has been due to a DDoS attack. It joins the long list of darknet services that have been hit by these recent attacks, which now appear to have mostly been based on the darknet markets being held for ransom by attackers. A string of articles on Deep Dot Web recently revealed the source of the issues. The truth was discovered when a market admin’s account was hacked by TheRealDeal, another marketplace, and the admin’s communication were revealed. It was back at the beginning of May when Mr Nice Guy was hit with DDoS attacks. The offenders demanded 8 bitcoins to be paid within an hour to end the assault; however, the admin had another plan in mind. He wanted to negotiate, and he was willing to pay. He offered the attackers $200 a day or $6000 a month to launch DDoS attacks against rival markets including Agora, Nucleus, BlackBank and AlphaBay. The reputation of Mr Nice Guy has surely been greatly damaged by these events. While there is a great deal of competition between darknet markets for the multitude of customers that seek to buy and sell on the Deep Web, in the past similar attacks have been met with collaboration. The darknet markets, though they compete with each other for business recognize the necessity for cooperation, as it only takes a few markets to go down for the integrity of all markets to be questioned. Nowhere was this more evident than when the Evolution marketplace exit scammed, leaving with over $12 million dollars in bitcoin. The aftermath revealed a dark spell of the darknet markets as they all suffered a reduction in customers. In an interview with Deep Dot Web, the man behind Mr Nice Guy spoke about his remorse for what he had done. He said that it would be up to the Deep Web community whether they wished to trust him again. However, he did say that he had learned that the way to attract customers was increasing security as well as providing extra services; he stated that his is the only major marketplace offered in more than one language. While the DDoS attacks are still occurring to an extent, the loss of their contractor has reduced the efforts of the offenders somewhat, and most of the darknet markets have come back online. Yet this saga has definitely shown the weaknesses that exist in the system, and how one stray admin can do an awful lot of damage to the entire network. Source: http://darkwebnews.com/news/ddos-attacks-continue-to-plague-darknet-markets/
Visit site:
DDoS Attacks Continue To Plague Darknet Markets

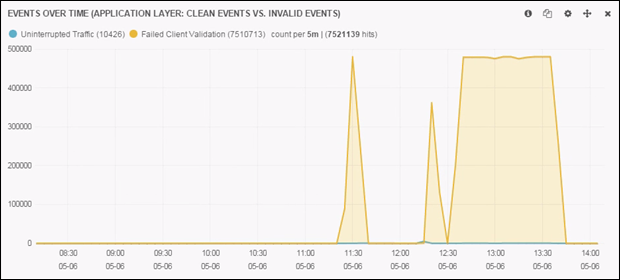
 In 2012, Anonymous introduced HOIC (high orbit ion cannon) as a replacement to LOIC (low orbit ion cannon). Unlike its predecessors, that were built upon C#, and later java. This new DDoS player was built upon the unsuspecting language of Visual Basic. Taught in high school classrooms, Visual Basic was largely seen by the programming community as a means for kids and young programmers to get their feet wet in the experience of programming. Considered by many programmers as grossly inefficient and a memory hog; Visual Basic was an unsuspected carrier for what would become one of the most powerful means of DDoS. One of the popular notions of HOIC has been its ability to randomize variables such as: user agent, referrer and URI, during an attack. In the same manner, an attack tool known as HULK (developed by: Barry Shteiman, 2012), written in Python, was developed in recent history. Within a controlled environment we tested these DDoS tools to judge their effectiveness and total output. In controlled trials the DDoS output of LOIC (Visual Basic on Windows) outperforms the DDoS output HULK (Python on Linux) by +40%. Figure 1: HOIC Test in Stable Windows Environment Figure 2: HULK Test While many of us in the Internet security industry ridicule and downplay the “kiddie hacker;” it is clear that it sometimes only takes a kiddie to build an empire. Lessons in open source economics teach us that in an open access environment, it takes only a small few to bring about radical change and innovation. Today HOIC has become one of the primary tools of groups such as anonymous. From this lesson, we can expect that challenges and sudden changes, will not come from those paid hundreds of thousands a year; but from those small few kiddies, whom are politically motivated and are paid nothing. Source: http://www.dosarrest.com/ddos-blog/how-visual-basic-broke-modern-python-welcome-to-the-world-of-high-orbit-ion-cannon/
In 2012, Anonymous introduced HOIC (high orbit ion cannon) as a replacement to LOIC (low orbit ion cannon). Unlike its predecessors, that were built upon C#, and later java. This new DDoS player was built upon the unsuspecting language of Visual Basic. Taught in high school classrooms, Visual Basic was largely seen by the programming community as a means for kids and young programmers to get their feet wet in the experience of programming. Considered by many programmers as grossly inefficient and a memory hog; Visual Basic was an unsuspected carrier for what would become one of the most powerful means of DDoS. One of the popular notions of HOIC has been its ability to randomize variables such as: user agent, referrer and URI, during an attack. In the same manner, an attack tool known as HULK (developed by: Barry Shteiman, 2012), written in Python, was developed in recent history. Within a controlled environment we tested these DDoS tools to judge their effectiveness and total output. In controlled trials the DDoS output of LOIC (Visual Basic on Windows) outperforms the DDoS output HULK (Python on Linux) by +40%. Figure 1: HOIC Test in Stable Windows Environment Figure 2: HULK Test While many of us in the Internet security industry ridicule and downplay the “kiddie hacker;” it is clear that it sometimes only takes a kiddie to build an empire. Lessons in open source economics teach us that in an open access environment, it takes only a small few to bring about radical change and innovation. Today HOIC has become one of the primary tools of groups such as anonymous. From this lesson, we can expect that challenges and sudden changes, will not come from those paid hundreds of thousands a year; but from those small few kiddies, whom are politically motivated and are paid nothing. Source: http://www.dosarrest.com/ddos-blog/how-visual-basic-broke-modern-python-welcome-to-the-world-of-high-orbit-ion-cannon/