DDoS attacks are often seen as a global phenomenon that affects ISPs and large datacentres. But the daily damage is done by much smaller attacks on vulnerable, sometimes poorly defended resources such as websites belonging to well-known organisations. The UK has had more than its fair share of such attacks with hacktivism and occasionally extortion the main motivations. Here we chart some of the worst attacks that have affected UK organisations in recent years. DoS attack on CMP Media (UBM) – 1998 Proof that simple denial of service (DoS) attacks (if not DDoS) are far from new, a disgruntled magazine subscriber decided to barrage the email server and fax machines of the UK tech publisher CMP Media (later sold to UBM) with enough traffic to cut the company off from the world for most of two days. The ISP identified the likely culprit but in 1998 denial of service attacks were a civil rather than criminal matter and remained so until 2006. LulzSec ‘”Tango down” DDoS attacks – 2011 The group that gave the Anonymous movement its UK brand, the small collection of mainly British youths that hid behind the LulzSec moniker loved their DDoS. Several big UK organisations were targeted but the attack that downed the Serious Organised Crime Agency (SOCA) website in June 2011 was probably the last straw. Alleged UK GCHQ DoS attack on Anonymous – 2011 In 2014 Britain hater and anti-NSA campaigning journalist Glenn Greenwald alleged that GCHQ Joint Threat Research Intelligence Group (JTRIG) unit launched DDoS attacks to disrupt chatrooms used by hacktivists from Anonymous and LulzSec. It was pointed out that this was really a targeted DoS attack and not an indiscriminate DDoS. Attack on the BBC by Iran – 2012 Downplayed at the time but what hit the Beeb on 2 March 2012 was anything but for those on the receiving end. Downed the BBC’s email server for a while, disrupted its Persian Service (hence the blame being attributed to Iran, which hates the Service’s output) and even overloaded its exchange with large numbers of phone calls. DDoS attack on Oxford and Cambridge universities – 2012 A single 20-year old individual – later imprisoned for a range of cybercrimes – was blamed for the DDoS attacks on Oxford and Cambridge University that disrupted their websites for a period of days in 2011 and 2012. It was never clear why the named man attacked the universities but the ease with which one person could cause so much trouble for large institutions was noted at the time. DDoS on 123-reg domain registrar – 2012 A sign that DDoS attacks could take on even big Internet-facing businesses, in May 2012 the UK’s largest domain registrar was hit with enough traffic to take its site down for a reported 15 minutes with further problems throughout the day. Rivals were also targeted as crybercriminals tested their latest techniques against well-defended businesses. Spamhaus 325Gbps super-DDoS – 2012 The massive 325Gbps DDoS attack on UK anti-spam organisation Spamhaus remains probably the second or third largest of all time and was even ridiculously said to have ‘slowed the Internet’. Later blamed on Dutch national Sven Kamphuis, the Spamhaus attack was the first to use a technique called DNS amplification to such sensational effect. Julian Assange hacktivists turn on MI5 – 2012 Wikileaks’ founder Julian Assange was briefly a focus for anti-corporate rage, and his pursuit by the UK, the US and Sweden over rape allegations promoted a series of hacktivist DDoS attacks in late 2012. Predictable they might have been but also surprisingly successful – MI5’s public website was put out of action for several hours. Manchester casino extortion attack – 2013 A rare publicised example of DDoS in the service of extortion, the attack on a Manchester-based online casino came after the business refused to pay the owner refused to hand over half the business to Polish nationals Piotr Smirnow and Patryk Surmacki. The pair were eventually arrested at Heathrow Airport tying to leave the country and later jailed. Raspberry Pi Foundation DDoS – 2013 Not everyone likes the Raspberry Pi people it seems including a “lone sociopath” with issues. The individual concerned launched a flurry of bizarre grudge DDoS attacks on its website, with some success. The attacker even targeted a group of teens working on a 48-hour Python hackathon using RaspBerry Pis. The Foundation beat the attacks with the help of an understanding ISP. Carphone Warehouse data breach DDoS – 2015 In July 2015, major UK smartphone retailer Carphone Warehouse suffered a serious data breach which, it later transpired, might have been aided using a DDoS ‘distraction’ attack. Up to one in five DDoS incidents are later found to be part of a data theft snatch in which IT staff are occupied fending off the DDoS, giving attackers more opportunity to sneak in and out. Mumsnet DDoS attack by @DadSecurity – 2015 Who would attack a site as apparently innocuous as Mumsnet? In what must rank as the oddest ideological attack of recent times, a campaign group called ‘@DadSecurity’ is suspected of doing just that as part of a wider campaign of nuisance that included having an armed police team dispatched to the house of founder Justine Roberts. Came after earlier data breach in 2014. Source: http://www.techworld.com/picture-gallery/security/uks-12-worst-ddos-attacks-hacktivism-extortion-plain-malice-3623767/#12
Continue reading here:
The UK’s 12 worst DDoS attacks Summarized – hacktivism, extortion and plain malice

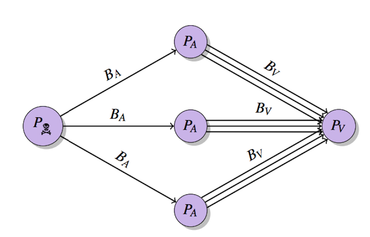
 The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic. A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale. At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks. Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system. In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit. During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request. This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power. City University London DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target. In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet. The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said: “An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim. The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.” In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team. In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times. Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/
The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic. A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale. At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks. Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system. In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit. During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request. This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power. City University London DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target. In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet. The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said: “An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim. The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.” In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team. In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times. Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/