The Winning Poker Network (WPN) was forced to cancel its $1 million guaranteed prize pool tournament on Sunday, after an apparent distributed denial-of-service (DDoS) attack caused disruptions and connectivity issues for players participating in the event. While the tournament had been running for several hours, late registration was still open, so all players were refunded their buy-ins and entry fees in accordance with network policy. The tournament was an ambitious effort by WPN, a network that includes America’s Cardroom, to bring a major online poker tournament to US players. It was billed as the first $1 million event in American online poker in nearly four years, as the events of Black Friday had more or less put an end to such prize pools in the country. Cancelled Despite Strong Turnout With a $500 + $40 buy-in and entry fee, the tournament needed 2,000 players to meet the prize guarantee (without dipping into the entry fees), and it appeared likely to do so. When the tournament was finally cancelled, 1,937 players had registered, and there were still about 45 minutes left in the late registration period. According to reports, the event was cancelled after less than five hours of play, though some players have said closer to 5.5 hours had elapsed by the time it was officially cancelled. Given how long the tournament had been running, a substantial number of players had already been eliminated; on the TwoPlusTwo.com forums, some players said they had hoped for some sort of chip split or ICM chop among the remaining players, given the large stacks they had accumulated in the first few hours of play. CEO Addresses Issues, Defends Decisions After the tournament, WPN CEO Phil Payton streamed a broadcast live on Twitch.tv to address the cancellation. “Call it a conspiracy, call it what you want, a lot of online poker sites have had Internet connectivity issues,” a clearly disappointed and frustrated Payton said. Payton referenced the fact that tournament issues were caused by DDoS attacks last weekend, but had seemed to clear up in the days before the big event. Whoever was causing the Internet disconnections was waiting for the million,” Payton said. “The second that it started, it started.” According to Payton, he and his staff initially tried to fight through it, but eventually came to the conclusion that it simply wasn’t fair to players who might be disconnected during key hands. “There’s a lot of sites that [would say] let them push through it, and we make $80,000, and gg,” Payton said. “Well, you know what, I’ve got to sleep with myself at night, and I’m not going to do that. “If it happened again tomorrow, I’d do the same thing,” he added. As Payton referenced, there have been an increasing number of DDoS attacks across online poker and the Internet at large. Just days earlier, players were suspicious about the possibility of DDoS attacks being used to disconnect opponents for the benefit of a specific player. Swedish operator Svenska Spel also had to cancel some poker tournaments last month following similar attacks and a massive Internet collapse in Sweden just last week is also blamed on DDoS hackers. In the end, given that the issues gave some players an advantage, Payton said that he was happy to stand by his decision, even if it was unpopular. “It doesn’t matter if you like it or not,” Payton said in response to questions about the decision at the end of his broadcast on Twitch. “It was fair.” Source: http://www.cardschat.com/news/wpn-1m-tournament-cxld-ddos-attack-8827
Read the original:
Winning Poker Network $1M Guaranteed Tournament Cancelled After Apparent DDoS Attack


 The Finest Squad is set out to bring cyber criminals to justice around the world; their main plan at the moment is to bring DDoS services down. When you visit the @FinestSquad Twitter account they are going all out with their tweets, you can clearly see they want the world to see they brought the Lizard Squad crew to their knees with its pinned tweet. Lizard Squad has been removed from twitter thanks to the Finest Squad, and then they say in their tweet, “Your welcome fellow gamers. We will make sure their IRC stays offline.” The next few steps for the Finest Squad include taking down / offline as many DDoS services, these include hosting, offshore, hosting, web booters and more. They have also announced on its Twitter account they are setting up a new YouTube channel, a news bulletin and a community forum – these are being developed right now so stay tuned. They also want to stack up its team; they basically want more of the finest. They do stress no illegal activities allowed, are you interested. This new role comes after they hired a professional full-time web designer/developer and web site security specialist. Looks like the Finest Squad is here to help all the gamers out there, PlayStation and Xbox gamers will be thrilled to bits Lizard Squad has had the Finest treatment. They do not like these kids harassing people and that is why they are there to bring justice. So far the Finest Squad website lists the LizardSquad member Obnoxious being arrested, @LizardPatrol, @LizardSquad and many more being removed from Twitter. All these wrong doings are being hunted, such as the EZTV proxy site being shutdown – read more here. Are you happy with what the Finest Squad have done so far? Source: http://www.onlinesocialmedia.net/20141217/finest-squad-to-bring-ddos-services-down/
The Finest Squad is set out to bring cyber criminals to justice around the world; their main plan at the moment is to bring DDoS services down. When you visit the @FinestSquad Twitter account they are going all out with their tweets, you can clearly see they want the world to see they brought the Lizard Squad crew to their knees with its pinned tweet. Lizard Squad has been removed from twitter thanks to the Finest Squad, and then they say in their tweet, “Your welcome fellow gamers. We will make sure their IRC stays offline.” The next few steps for the Finest Squad include taking down / offline as many DDoS services, these include hosting, offshore, hosting, web booters and more. They have also announced on its Twitter account they are setting up a new YouTube channel, a news bulletin and a community forum – these are being developed right now so stay tuned. They also want to stack up its team; they basically want more of the finest. They do stress no illegal activities allowed, are you interested. This new role comes after they hired a professional full-time web designer/developer and web site security specialist. Looks like the Finest Squad is here to help all the gamers out there, PlayStation and Xbox gamers will be thrilled to bits Lizard Squad has had the Finest treatment. They do not like these kids harassing people and that is why they are there to bring justice. So far the Finest Squad website lists the LizardSquad member Obnoxious being arrested, @LizardPatrol, @LizardSquad and many more being removed from Twitter. All these wrong doings are being hunted, such as the EZTV proxy site being shutdown – read more here. Are you happy with what the Finest Squad have done so far? Source: http://www.onlinesocialmedia.net/20141217/finest-squad-to-bring-ddos-services-down/ 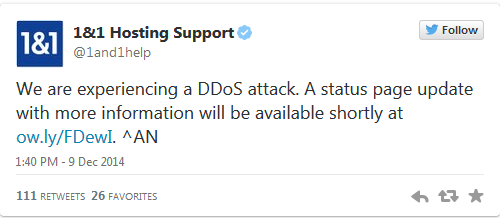
 UK hosting company 1&1 went titsup late on Tuesday night and struggled to recover this morning, after claiming it had been the victim of a Distributed-Denial-of-Service (DDoS) attack. The website collapsed shortly before 10pm yesterday, and it has taken 1&1 a full 12 hours to get its service back up and running. Readers who told the Reg about the outage said that the service had been flaky for several hours before it keeled over. 1&1 blamed the downtime on a DDoS attack in a tweet. However, although the website appeared to be returning to normal, 1&1 had yet to update its customers about the status of its system at time of writing. Customers were still griping about the mysterious outage this morning. Indeed, 1&1 was tight-lipped about the cause of the service disruption on its status page, which made no mention of a system security breach. Last month, Fasthosts blamed a five-hour outage it had suffered on a DDoS attack. Source: http://www.theregister.co.uk/2014/12/10/1_and_1_hosting_firm_claims_ddos_attack_downs_website/
UK hosting company 1&1 went titsup late on Tuesday night and struggled to recover this morning, after claiming it had been the victim of a Distributed-Denial-of-Service (DDoS) attack. The website collapsed shortly before 10pm yesterday, and it has taken 1&1 a full 12 hours to get its service back up and running. Readers who told the Reg about the outage said that the service had been flaky for several hours before it keeled over. 1&1 blamed the downtime on a DDoS attack in a tweet. However, although the website appeared to be returning to normal, 1&1 had yet to update its customers about the status of its system at time of writing. Customers were still griping about the mysterious outage this morning. Indeed, 1&1 was tight-lipped about the cause of the service disruption on its status page, which made no mention of a system security breach. Last month, Fasthosts blamed a five-hour outage it had suffered on a DDoS attack. Source: http://www.theregister.co.uk/2014/12/10/1_and_1_hosting_firm_claims_ddos_attack_downs_website/