A month before Pakistan’s ceasefire violation on the eve of Independence Day, a silent battle was raging in Mumbai’s financial district. Two large private banks, a retail brokerage and a state-owned lender faced a cyberattack from hackers across the border that seriously slowed down all online customer transactions. In the world of cybercrime, such attacks, which could be mistaken as normal traffic overload on the Net, are known as ‘distributed denial of service’ or DDoS. Spread across the world, hackers, either sympathetic to lost causes or indulging in the game of extortion, virtually ‘take over’ thousands of computers in diverse destinations before unleashing a DDoS strike. As computers that are hacked into start behaving as robots – or, ‘botnet’ in cyberparlance, the hackers divert traffic from these terminals to clog the systems of targets like banks and even e-commerce firms. A bank that is invaded may be unaware of the attack and even take a while to sense that customers are struggling to put through a simple net banking fund transfer or credit card payment. The July attack On that day in July, it was no different. The financial institutions received advisory on the DDoS attack from the government’s Computer Emergency Response Team (CERT). Also, there were alerts that more attacks could follow over the next few hours, said a cybercrime expert. Speaking to ET on condition of anonymity , one of the senior most officials in the government’s cybersecurity establishment said, “There was an attack but this was effectively countered. Often these things are done with the intention to blackmail … But we have the systems to handle it. There have been finance ministry and RBI instructions to banks for taking necessary measures to protect against DDoS strikes.” According to cybersecurity head in one of the largest Indian banks, since April there have been several advisories from government agencies like CERT and National Critical Information Infrastructure Protection Centre on DDoS. “In a DDoS attack, if a bank can block the bogus traffic diverted by a hacker for the first 15 minutes, then the attacker typically moves away to a weaker target. But if an institution is unable to resist, then the attacker may demand ransom. Rogue hackers in places like Nigeria and East Europe want to be paid in Bitcoin. Since Bitcoin is based on what is known as block-chain technology, fund transfers leave no trail.” Safety measures As precaution, no bank, to begin with, should depend on a single internet service provider (ISP), he said. “Besides, banks are beginning to invest in anti-DDOS high-end appliances. Some are carrying out mock drills to test the technology. Here, a flood of traffic is diverted to banks’ own websites to figure out whether the ISP and banks’ internal cybersecurity teams are adequately alert,” said the banker who refused to be named. Until a hack attack is obvious, companies in India typically keep such incidents under wrap as regulators do not insist on mandatory reporting of security breach. Some of the US-listed Indian entities are even more reticent: Since a cyberattack is rarely disclosed due to fear that it could scare away customers, it becomes more difficult to admit the breach later. In DDoS attack, including the current one, there is no data compromise or cash theft. “The timing of the event suggests that it could be handiwork of some of the Pakistani hackers who may be located in the US and Europe. Typically, they are active before big festivals or in the run up to Independence Day or Republic Day. They have a specific point to prove,” said an ethical hacker, who advises several companies and agencies on cybersecurity . Types of hackers According to him, there are three broad types of hackers, differentiated by motives. First, the financially motivated cybercriminal, who are usually from Eastern Europe and are interested in stealing credit card information, or engage in identity theft etc. They are highly organized, infect thousands of systems across the globe in order to achieve their objectives, and even ‘rent’ access to an infected computer for an hourly fee for conducting DDoS. The second type are hacktivists or politically motivated hackers whose sole interest is in furthering a political agenda by defacing a site, or bringing a site down through DDoS attacks. Pakistani hackers fall in this category . The third and the most serious type are nation state attackers involved in corporate espionage. They gain access to competing companies in order to steal business strategy and intellectual property. Chinese hackers are well-known for this. Source: http://timesofindia.indiatimes.com/tech/tech-news/Prepare-a-new-dossier-Pakistans-cyber-Mujahideen-hit-India/articleshow/48739013.cms?
View post:
Prepare a new dossier! Pakistan’s cyber Mujahideen hit India

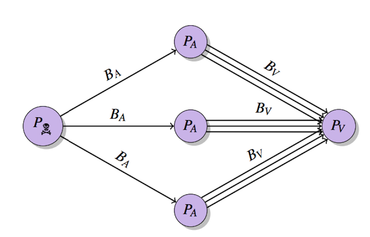
 The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic. A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale. At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks. Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system. In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit. During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request. This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power. City University London DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target. In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet. The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said: “An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim. The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.” In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team. In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times. Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/
The technology is vulnerable to exploit in launching a breed of DDoS attack which reflects and amplifies traffic. A flaw in BitTorrent clients can be exploited to allow single attackers to harness extra juice in launching DDoS attacks on a vast scale. At the USENIX conference in Washington, D.C., researchers from City University London unveiled ways that BitTorrent-based programs including uTorrent, Mainline and Vuze are vulnerable to distributed reflective denial-of-service (DRDoS) attacks. Specifically, cyberattackers can exploit protocols used by BitTorrent — a popular way of sharing large files online through peer-to-peer networking — to reflect and amplify traffic from other users in the system. In a paper dubbed “P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Reflective DoS Attacks,” the research team says the protocol family used by BitTorrent — Micro Transport Protocol (uTP), Distributed Hash Table (DHT), Message Stream Encryption (MSE))and BitTorrent Sync (BTSync) — are all vulnerable to exploit. During testing, over 2.1 million IP addresses were crawled and 10,000 BitTorrent handshakes were analyzed within a P2P lab test environment. The City University London researchers were able to assault a third-party target through traffic amplified up to a factor of 50 times, and in case of BTSync, up 120 times the size of the original request. This means that a lone attacker could exploit the system to conduct attacks on websites and companies far more debilitating than their actual computational power. City University London DRDoS cyberattacks hook in slave machines to participate in distributed denial of service (DDoS) attacks without user consent or knowledge. Traffic requests sent from victim systems are redirected which sends additional traffic to the target. In turn, this can result in websites and online services unable to cope with a flood of requests, denying access to legitimate users and taking sites offline until the flow of traffic dissipates — all caused with fewer slave machines and without the cost of hiring out a botnet. The BitTorrent protocols do not include processes to prevent IP address spoofing, which means an attacker can use peer-discovery methods including trackers, DHT or Peer Exchange (PEX) to collect millions of possible amplifiers for their DRDoS attacks. The researchers said: “An attacker which initiates a DRDoS does not send the traffic directly to the victim; instead he/she sends it to amplifiers which reflect the traffic to the victim. The attacker does this by exploiting network protocols which are vulnerable to IP spoofing. A DRDoS attack results in a distributed attack which can be initiated by one or multiple attacker nodes.” In addition, “the most popular BitTorrent clients are the most vulnerable ones,” according to the team. In March, code repository GitHub suffered a debilitating DDoS attack, the largest in the website’s history which lasted for days. Believed to originate from China, the DDoS attack involved a wide combination of attack vectors, sophisticated techniques and the use of unsuspecting victim PCs to flood GitHub with traffic in order to push GitHub to remove content from anti-censorship organization Greatfire.org and publication the New York Times. Source: http://www.zdnet.com/article/bittorrent-exploits-allow-lone-attackers-to-launch-large-ddos-attacks/