Could you pass up a $40,000 return on a $20 investment? Odds are you couldn’t if you enjoy wreaking havoc on a business. New research released today by Incapsula shows distributed denial of service (DDoS) assaults continue to be expensive nuisances for online businesses — and that the attacks can be launched from botnets-for-hire for around $38 a month. A DDoS attack costs a business $40,000 per hour in terms of lost business opportunities, loss of consumer trust, data theft, intellectual property loss and more, Incapsula estimates. When you consider top attacks last for days and that half of all targets are repeatedly hit, it’s easy to see how quickly costs escalate. A Lot for a Little “What is most disconcerting is that many of these smaller assaults are launched from botnets-for-hire for just tens of dollars a month. This disproportion between attack cost and damage potential is the driving force behind DDoS intrusions for extortion and vandalism purposes,” the security firm noted in its 2015 DDoS Threat Landscape Report (registration required). Last year Incapsula reported a 240 percent increase in DDoS activity. This year, although DDoS activity is still rising, Incapsula highlighted shifts in the methods, length and types of attacks. Incapsula defines an attack as a persistent DDoS event against the same target (IP address or domain). It is preceded by a quiet (attack free) period of at least 10 minutes and succeeded by another such period of the same duration or longer. The study differentiates between network layer and application layer attacks. These definitions refer to the Open Systems Interconnection model (OSI Model), which conceptualizes the process of data transmission by segmenting packets into seven layers. Network layer attacks target the network and transport layers (OSI layers 3 and 4), while application layer attacks target OSI layer 7. The analysis is based on data from 1,572 network layer and 2,714 application layer DDoS attacks on websites using Imperva Incapsula services from March 1 through May 7. “Assaults against network infrastructures continue to grow in size and duration. Those aimed at applications are both long in duration and likely to be repetitive. The upshot for organizations of all sizes is that simply weathering the storm is no longer a viable strategy — the impact will be big, durable and likely recurring,” the report notes. On That Depressing Note Here are a few of the report’s key findings: Once a target, always a target: 20 percent of websites are attacked more than five times DDoS attacks can last a long time: While 71 percent of all network layer attacks last under three hours, more than 20 percent last more than five days Some attacks are exceptionally long: The longest attack was 64 days DDoS for hire is more readily available than ever: Botnet-for-hire fingerprints are on roughly 40 percent of all attacks Five countries create most DDoS botnet traffic : 56 percent of DDoS bot traffic emerged from China, Vietnam, US, Brazil and Thailand What’s a Botnet-for-Hire? Opportunistic cybercriminals have the botnet-for-hire business model, a subscription scheme that provides each user with limited access to the botnet resources (usually for a cumulative duration of no more than 60 minutes per month). “During these short periods, individuals with little or no DDoS skill are able to execute assaults using one of the few available scripts (which are reminiscent of our definition of attack vectors),” the report notes. The average cost to rent-a-botnet for an hour each month through a DDoS subscription package is around $38, with fees as low as $19.99. The takeaway: It costs very little to bring down a website. “Perhaps putting a price tag on the damage caused by such services will bring more public attention to their activity, and to the danger posed by the shady economy behind DDoS attacks,” the report notes. Source: http://www.cmswire.com/information-management/you-can-bring-down-a-website-for-38/
Continue Reading:
Cost to launch DDoS attack from botnets for hire

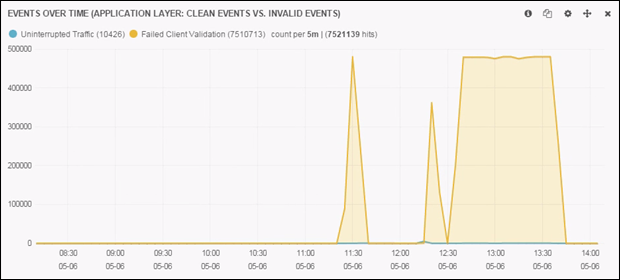
 In 2012, Anonymous introduced HOIC (high orbit ion cannon) as a replacement to LOIC (low orbit ion cannon). Unlike its predecessors, that were built upon C#, and later java. This new DDoS player was built upon the unsuspecting language of Visual Basic. Taught in high school classrooms, Visual Basic was largely seen by the programming community as a means for kids and young programmers to get their feet wet in the experience of programming. Considered by many programmers as grossly inefficient and a memory hog; Visual Basic was an unsuspected carrier for what would become one of the most powerful means of DDoS. One of the popular notions of HOIC has been its ability to randomize variables such as: user agent, referrer and URI, during an attack. In the same manner, an attack tool known as HULK (developed by: Barry Shteiman, 2012), written in Python, was developed in recent history. Within a controlled environment we tested these DDoS tools to judge their effectiveness and total output. In controlled trials the DDoS output of LOIC (Visual Basic on Windows) outperforms the DDoS output HULK (Python on Linux) by +40%. Figure 1: HOIC Test in Stable Windows Environment Figure 2: HULK Test While many of us in the Internet security industry ridicule and downplay the “kiddie hacker;” it is clear that it sometimes only takes a kiddie to build an empire. Lessons in open source economics teach us that in an open access environment, it takes only a small few to bring about radical change and innovation. Today HOIC has become one of the primary tools of groups such as anonymous. From this lesson, we can expect that challenges and sudden changes, will not come from those paid hundreds of thousands a year; but from those small few kiddies, whom are politically motivated and are paid nothing. Source: http://www.dosarrest.com/ddos-blog/how-visual-basic-broke-modern-python-welcome-to-the-world-of-high-orbit-ion-cannon/
In 2012, Anonymous introduced HOIC (high orbit ion cannon) as a replacement to LOIC (low orbit ion cannon). Unlike its predecessors, that were built upon C#, and later java. This new DDoS player was built upon the unsuspecting language of Visual Basic. Taught in high school classrooms, Visual Basic was largely seen by the programming community as a means for kids and young programmers to get their feet wet in the experience of programming. Considered by many programmers as grossly inefficient and a memory hog; Visual Basic was an unsuspected carrier for what would become one of the most powerful means of DDoS. One of the popular notions of HOIC has been its ability to randomize variables such as: user agent, referrer and URI, during an attack. In the same manner, an attack tool known as HULK (developed by: Barry Shteiman, 2012), written in Python, was developed in recent history. Within a controlled environment we tested these DDoS tools to judge their effectiveness and total output. In controlled trials the DDoS output of LOIC (Visual Basic on Windows) outperforms the DDoS output HULK (Python on Linux) by +40%. Figure 1: HOIC Test in Stable Windows Environment Figure 2: HULK Test While many of us in the Internet security industry ridicule and downplay the “kiddie hacker;” it is clear that it sometimes only takes a kiddie to build an empire. Lessons in open source economics teach us that in an open access environment, it takes only a small few to bring about radical change and innovation. Today HOIC has become one of the primary tools of groups such as anonymous. From this lesson, we can expect that challenges and sudden changes, will not come from those paid hundreds of thousands a year; but from those small few kiddies, whom are politically motivated and are paid nothing. Source: http://www.dosarrest.com/ddos-blog/how-visual-basic-broke-modern-python-welcome-to-the-world-of-high-orbit-ion-cannon/