It’s time your IT department rebelled against the cybercrime empire, says Srinivasan CR, VP of global product management, data centre services at Tata Communications Distributed Denial of Service (DDoS) attacks have been making a lot of headlines in the last year – particularly through the work of the Lizard Squad, the cyber criminals behind the attacks that caused major network outages for global corporations such as Microsoft, Sony and Malaysian Airlines. While only the severest attacks affecting some of the highest profile businesses might make the news, cyber criminals are launching new DDoS attacks on a daily basis. Large enterprises such as carriers and online retailers – who rely on the web to sell their products and services and to engage with their customers – are often under relentless bombardment. Furthermore, the financial and reputational implications of DDoS attacks are growing in significance. Companies face the threat of not only losses inflicted by operational downtime, but also of extortion from the more recent phenomenon of ‘ransom attacks’. Attack of the Clones – Forming a Botnet Army DDoS attacks rely on hijacked devices that cyber criminals add to their army, bombarding a weakness in a network. Infected devices are turned into robots, called botnets, which add network traffic to the attack. This is akin to recruiting an army of clones formed by specific computers, ports or services on the target system, entire networks or network and system components. The most common type of DDoS attack involves flooding the target with external communications requests. Eventually, the attack will build enough momentum to bring the network to a standstill, as it can no longer deal with the wave of requests. It is comparable to a global ticketing website crashing on the day Beyoncé tour tickets go on sale due to unmanageable traffic demand. Both scenarios can lead to significant financial losses and damage client and customer relationships, as mission critical systems and business operations grind to a halt. One of the reasons DDoS protection is climbing higher up the IT agenda is that this form of cyber attack is growing in sophistication. By exploiting vulnerabilities in unprotected networks and a range of connected devices, including smartphones and tablets, DDoS attackers are able to grow their botnets at an alarming rate. This increases the scale and power of an attack and reduces the likelihood of an effective counter attack from the victim’s network. This also gives cyber criminals more control over the timing of an attack. For example, staging a successful attack at a crucial time when a business simply cannot afford for its networks to fall over gives attackers far more leverage. Furthermore, while DDoS attacks are not, strictly speaking, to be confused with hacking, which involves infiltrating a network rather than simply choking it into submission, the two can be combined to devastating effect. A successful DDoS attack can render the network operator powerless to protect their systems, making them more susceptible to a full-scale network breach. Consequently, there have recently been examples of companies effectively being held to ransom under the threat of a DDoS attack in exchange for sums of bitcoin and other forms of extortion. Organisations such as carriers, online retailers and financial service platforms are heavily reliant on their global online presence to do their day-to-day business and remain profitable. Therefore, the threat of a powerful DDoS attack, particularly around a significantly busy trading period, gives cyber criminals additional leverage, which may persuade the target organisation to hand over significant sums to avoid being attacked. A New Hope – Scrubbing the Network Clean Given the nature of DDoS attacks, the best form of defence is attack. Rather than waiting for attacks to hit your network and relying on the ability of your security system to stand up to them, best practice is to anticipate them, and deal with them in real-time. This process is known as scrubbing. Designated scrubbing centres take care of the heavy lifting when it comes to mitigating and breaking up attacks. Scrubbing ensures the network layers act as the first line of defence. Incoming traffic is monitored and cleansed in real-time. Clean traffic is then routed into the network, whereas traffic that is considered threatening is routed back to the source. This approach means that legitimate traffic always gets through, and malicious traffic is mitigated at the source rather than near the target network, so it does not choke bandwidth. For example, Tata Communications has 15 scrubbing centres across the globe. A team of skilled engineers monitor attacks close to the botnet and DDoS heatmap. The attack is broken down in manageable chunks rather than tackled when it has gathered too much momentum. Yet, scrubbing should only be considered the first line of defence. IT managers also have monitoring proxy services, network and web application firewalls, VPN protection and securing virtual gateways to think about. Ideally, these should be delivered as part of a comprehensive managed security service. This can be achieved by delivering security services from the cloud, giving IT managers greater flexibility and choice in terms of the services and pricing models available to them. Providing security as a managed service with cloud-based solutions such as Distributed Denial of Service as a Service (DDoSaaS), Firewall as a Service (FwaaS), Virtual Private Network as a Service (VPNaaS) and Security Information and Event Management as a Service (SIEMaaS) has numerous benefits for businesses. As well as the peace of mind of knowing that all aspects of security are being proactively managed by a team of dedicated experts, a managed security service also gives IT managers a single point of contact for their security needs. This removes the administrative strain of multiple contracts, and the prospect of being passed around the houses when trying to solve a problem. Keeping the Peace – Neutralising the DDoS Threat DDoS attacks are becoming increasingly sophisticated and malicious, as cyber criminals hold businesses to ransom, threatening to bring corporate networks down for days or even for weeks. Yet, best practice to fight DDoS follows common security rules of thumb. As with any type of cyber threat, enterprises should expect to be hit by a DDoS attack, so preventative measures are key. Protecting the network is a living, breathing operation – you need to constantly seek out the next DDoS wave on the network and strike back before your business comes under attack. Source: http://www.techweekeurope.co.uk/security/ddos-wars-network-strikes-back-171925
Read More:
DDoS Wars: The Network Strikes Back


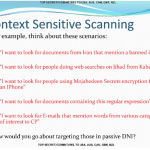 XKeyscore runs on Linux-based servers across 150 field sites scattered across the globe. No matter what you’ve done on the internet, you can bet the National Security Agency has a record of it. Newly released documents leaked by Edward Snowden shed light on the scale and scope of the XKeyscore program, a program described by one classified document as the “widest-reaching” system for gathering information from the internet. The new batch of documents detail one of the most extensive programs used in the US government’s arsenal on global surveillance, more than two years after it was first revealed by The Guardian . The program, which runs on hundreds of Red Hat Linux-based servers scattered around the globe (likely in US Embassy buildings), allows analysts to filter the vast amount of incidental data created when a user browses the web. The program allows analysts to selectively pick out usernames and passwords, browser history, emails sent and received, social media data, and even locations and detect whether or not a computer is vulnerable to certain kinds of malware or other threats. A single unique identifier, such as a username, password, email fragment, or even images, can be used to trace a person’s online activities with extreme precision. One of the documents said the program was successful in capturing 300 terrorists based on intelligence it had collected. Out of all the programs, XKeyscore may be the largest in scope, with some field sites sifting through more than 20 terabytes of data per day, according to The Intercept , collected from the various fiber cables around the world. The newly-released trove of documents details a broader scope of access to personal information that NSA analysts have. Those include: The NSA was able to acquire talking points UN Secretary General Ban Ki-moon wanted to bring up with US President Barack Obama through the Blarney program, which feeds the XKeyscore program. (Blarney is thought to be a program that taps fiber optic cables at core internet choke points around the US and the world.) When a group of people overload a server or network with a flood of network traffic (causing a “distributed denial-of-service” or DDoS attack), users can be identified using XKeyscore. One document boasts of how “criminals” can be found through the program. NSA analysts can plug in queries such as “show me all the exploitable machines in [whichever] country” and have returned to them a list of computers and devices that are vulnerable to the hacking exploits of the NSA’s elite intrusion unit, known as Tailored Access Operations (TAO). That also extends to “find all iPhones in Nigeria,” or “find Germans living in Pakistan.” One of the documents showing how NSA analysts can use XKeyscore Oversight of the program is limited at best. The system is littered with reminders not to breach human rights’ laws or minimization procedures designed to prevent Americans’ data from being used by the program. Yet, not everything is audited. System administrators often log in to the program under one username, “oper,” which is used across multiple people and divisions, making any actions carried out under that name almost impossible to track. XKeyscore can search other databases, like Nucleon, which “intercepts telephone calls and routes the spoken words” to a database. (So yes, the US government is listening to some people’s phone calls.) One newly-released document showed more than 8,000 people are ensnared by the program, with more than half-a-million voice files recorded each day. An al-Qaeda operative is said to have searched Google for his own name, among other aliases, which was picked up by the XKeyscore program, another document shows . The program is able to snoop inside documents attached to emails, one document says . That supposedly can help determine who had authored a Word or PowerPoint document. NSA has its own internal online newspaper, a document shows , which the agency dubs the “NSA Daily.” It’s a top secret publication, which only agents belonging to UK, US, Australian, Canadian, and New Zealand intelligence agencies can access. The NSA said in a statement (of which portions had been used in previous statements) that its foreign intelligence operations are “authorized by law” and are “subject to multiple layers of stringent internal and external oversight.” Source: http://www.zdnet.com/article/nsa-xkeyscore-spy-united-nations-target-denial-service-more/
XKeyscore runs on Linux-based servers across 150 field sites scattered across the globe. No matter what you’ve done on the internet, you can bet the National Security Agency has a record of it. Newly released documents leaked by Edward Snowden shed light on the scale and scope of the XKeyscore program, a program described by one classified document as the “widest-reaching” system for gathering information from the internet. The new batch of documents detail one of the most extensive programs used in the US government’s arsenal on global surveillance, more than two years after it was first revealed by The Guardian . The program, which runs on hundreds of Red Hat Linux-based servers scattered around the globe (likely in US Embassy buildings), allows analysts to filter the vast amount of incidental data created when a user browses the web. The program allows analysts to selectively pick out usernames and passwords, browser history, emails sent and received, social media data, and even locations and detect whether or not a computer is vulnerable to certain kinds of malware or other threats. A single unique identifier, such as a username, password, email fragment, or even images, can be used to trace a person’s online activities with extreme precision. One of the documents said the program was successful in capturing 300 terrorists based on intelligence it had collected. Out of all the programs, XKeyscore may be the largest in scope, with some field sites sifting through more than 20 terabytes of data per day, according to The Intercept , collected from the various fiber cables around the world. The newly-released trove of documents details a broader scope of access to personal information that NSA analysts have. Those include: The NSA was able to acquire talking points UN Secretary General Ban Ki-moon wanted to bring up with US President Barack Obama through the Blarney program, which feeds the XKeyscore program. (Blarney is thought to be a program that taps fiber optic cables at core internet choke points around the US and the world.) When a group of people overload a server or network with a flood of network traffic (causing a “distributed denial-of-service” or DDoS attack), users can be identified using XKeyscore. One document boasts of how “criminals” can be found through the program. NSA analysts can plug in queries such as “show me all the exploitable machines in [whichever] country” and have returned to them a list of computers and devices that are vulnerable to the hacking exploits of the NSA’s elite intrusion unit, known as Tailored Access Operations (TAO). That also extends to “find all iPhones in Nigeria,” or “find Germans living in Pakistan.” One of the documents showing how NSA analysts can use XKeyscore Oversight of the program is limited at best. The system is littered with reminders not to breach human rights’ laws or minimization procedures designed to prevent Americans’ data from being used by the program. Yet, not everything is audited. System administrators often log in to the program under one username, “oper,” which is used across multiple people and divisions, making any actions carried out under that name almost impossible to track. XKeyscore can search other databases, like Nucleon, which “intercepts telephone calls and routes the spoken words” to a database. (So yes, the US government is listening to some people’s phone calls.) One newly-released document showed more than 8,000 people are ensnared by the program, with more than half-a-million voice files recorded each day. An al-Qaeda operative is said to have searched Google for his own name, among other aliases, which was picked up by the XKeyscore program, another document shows . The program is able to snoop inside documents attached to emails, one document says . That supposedly can help determine who had authored a Word or PowerPoint document. NSA has its own internal online newspaper, a document shows , which the agency dubs the “NSA Daily.” It’s a top secret publication, which only agents belonging to UK, US, Australian, Canadian, and New Zealand intelligence agencies can access. The NSA said in a statement (of which portions had been used in previous statements) that its foreign intelligence operations are “authorized by law” and are “subject to multiple layers of stringent internal and external oversight.” Source: http://www.zdnet.com/article/nsa-xkeyscore-spy-united-nations-target-denial-service-more/