Jay Radcliffe freaked out the medical community in 2011 when he revealed how insulin pumps could be hacked to deliver a fatal dose of insulin (pdf). Yet at a medical device security and privacy roundtable discussion at Black Hat, Radcliffe said “it would be far easier and more likely for an attacker to sneak up behind him and deliver a fatal blow to his head with a baseball bat,” than hack his insulin pump to kill him. He did discuss hacking implantable medical devices. There are no known cases of hacking a pacemaker in anything other than fiction, but if an attacker remotely hacked a pacemaker, no one is going to dig into the death. It would be called a heart attack and that would be the end of it because “there’s no process in place right now that checks these implanted medical devices for failure or malicious activity.” Rapid7 point out, “Security often just isn’t on the radar at all for the manufacturers, the pharmaceutical regulators, or even the medical professionals that work with them.” The term “medical device” could mean a broad range of things from pacemakers to “MRI machines and echo-cardiograms and computers in the hospital running Windows XP. Mobile apps and health-related consumer-focused applications could also be considered under this broad umbrella.” John Pescatore, who previously worked at the NSA and at the U.S. Secret Service before joining SANS, released a whitepaper based on a survey about Internet of Things security. Medical machinery and personal implanted medical devices are considered to be part of the IoT. After all, people can use SHODAN to find fetal heart monitors if they are so inclined. Pescatore wrote: Internet-connected computing capabilities related to smart building and industrial control systems and medical devices were the most commonly cited concerns after consumer devices. While these type of devices don’t receive much hype with respect to the IoT in the press, the use of embedded computing in those devices (versus layered operating systems and applications in PCs and servers that IT is accustomed to managing and securing) will cause major breakage in existing IT management and IT security visibility, vulnerability assessment, configuration management and intrusion prevention processes and controls. SANS also looked at cyberthreat intelligence provided by Norse and then published a whitepaper about “Widespread Compromises Detected, Compliance Nightmare on Horizon.” Norse analyzed over 100 terabytes of daily traffic and determined there were 49,917 unique malicious events, 723 unique malicious source IP addresses and 375 U.S.-based compromised health care-related organizations. “There are many reasons why these findings are cause for alarm,” wrote Barbara Filkins. One example was: “The sheer volume of IP addresses detected in this targeted sample can be extrapolated to assume that there are, in fact, millions of compromised health care organizations, applications, devices and systems sending malicious packets from around the globe.” Those aren’t the only threats. If a person was in cardiac arrest, a defibrillator could be used to save that person’s life. But what if someone who was not authorized to use or to tweak the defibrillator settings, did so? That may be unlikely, but not impossible. Default usernames and passwords for medical devices are problematic and are “often overlooked endpoints;” they “can be easily procured by an Internet search on ‘type of device’ plus ‘default password’.” Yesterday, the National Vulnerability Database published two advisories regarding ZOLL Defibrillators. The accompanying documents from the manufacturer describe how to change default configurations on the devices. CVE-2013-7395 states: “ZOLL Defibrillator / Monitor X Series has a default (1) supervisor password and (2) service password, which allows physically proximate attackers to modify device configuration and cause a denial of service (adverse human health effects).” CVE-2007-6756 states: “ZOLL Defibrillator / Monitor M Series, E Series, and R Series have a default password for System Configuration mode, which allows physically proximate attackers to modify device configuration and cause a denial of service (adverse human health effects).” So who is responsible for deploying the fix? The FDA guidance suggests that both hospitals and manufacturers are responsible for vulnerability management. Yet Radcliffe said that makes the problem of deploying patches even more murky. He explained that “if there is a bug in an MRI machine, the hospital will have to pay to have the manufacturer come in and update all the affected machines. Of course, the hospital could install the updates themselves, but they run the risk of losing their warranty. The hospital could also decide they don’t have the budget available to pay to have the patches installed and merely wait.” Those defibrillators are not the only machines that with default passwords that potentially pose a risk. “Most devices have no security applications on them at all. Anyone can just get in and manipulate whatever they want,” stated an unnamed hospital chief information security officer in a McKinsey Report. Forbes looked into how a network-attached printer using the defaults of “admin” and “12345” for a password could be a “near perfect and silent entry point” for hackers. Lastly, Radcliffe addressed how more security on medical devices could cause patients to have less privacy. For example, if a person with an implantable medical device were to die, then “who can look at a log of his or her health before death? That’s a serious privacy concern, but what if it helps doctors find issues with IMDs, or detect evidence of foul play such as hacking?” Source: http://www.networkworld.com/article/2464010/microsoft-subnet/attacker-could-use-default-defibrillator-password-to-launch-denial-of-service.html
View post:
Attacker could use default defibrillator password to launch DDoS attack


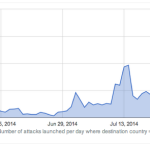 As conflict between Israel and the Palestinian militant Islamist organisation Hamas escalates, new research has revealed the impact politics has had on cyberattack trends. Tension between countries and changing political landscapes can now often be linked to cybercrime campaigns worldwide. From constant spats between the US and China to increased targeting of Syrian and Thai targets during political unrest, digital weaponry is now a key tool for groups to broadcast their own political messages, spy on governmental agencies and steal valuable data. In a new report released by Arbor Networks, anonymized traffic and DDoS attack data from over 290 ISPs that have deployed Arbor’s Peakflow SP product — collated and analyzed as part of Arbor’s ATLAS initiative — it appears that DDoS attacks are rising in number and volume as a result of the Israel-Hamas conflict. The graph below depicts the number of reported DDoS attacks initiated against Israel daily over the 1 June to 3 August period this year: Distributed Denial of Service (DDoS) attacks are used to flood a website or service with traffic to the point systems cannot cope, denying other users access to the website. Arbor detected a rise in the number of DDoS attacks targeting Israel in the first week of July, going from an average of 30 attacks per day to an average of 150 attacks initiated per day in July — peaking at 429 attacks on July 21st. Linking these cyberattacks to political situations, 30 June is when Israel publicly attributed the deaths of three kidnapped Israeli teenagers to Hamas, and on 7 July, “Operation Protective Edge” was launched by the country. As the political conflict raged on, so did the frequency of DDoS attacks until a drop occurred on 28 July lasting through 2 August. Arbor says the drop in attacks roughly correlates with cease fire talks which began 27 July. From 28 July through 2 August, there were 192 attacks recorded in total. On 3 August, the number of DDoS attacks rose sharply, with 268 attacks in total. In addition to the number of DDoS attacks over these time periods, the security researchers also noticed an increase in the peak size of these attacks. In the graph below, we can see that in June, no attacks exceeded 12Gbps. In July, seven DDoS attacks exceeded this size, with the largest peaking at 22.56Gbps on 12 July. When cease-fire talks fell apart on 3 August, the largest DDoS attack was recorded at a size of 29Gbps. The duration of DDoS attacks has also increased. In June, the average duration was 20 minutes — with a peak duration of 24 hours — and in July, the average duration was 1 hour 39 minutes. “As the intensity of the Israeli-Hamas conflict has increased, so has the number, size and duration of the DDoS attacks targeting Israel,” the researchers say. “Additionally, it even appears as if the attackers have made an effort to adhere to the “real world” calls for a cease-fire, resuming their attacks when the cease fire fell through.” Source: http://www.zdnet.com/israel-hamas-conflict-sparks-surge-in-ddos-attacks-7000032375/#ftag=RSS14dc6a9
As conflict between Israel and the Palestinian militant Islamist organisation Hamas escalates, new research has revealed the impact politics has had on cyberattack trends. Tension between countries and changing political landscapes can now often be linked to cybercrime campaigns worldwide. From constant spats between the US and China to increased targeting of Syrian and Thai targets during political unrest, digital weaponry is now a key tool for groups to broadcast their own political messages, spy on governmental agencies and steal valuable data. In a new report released by Arbor Networks, anonymized traffic and DDoS attack data from over 290 ISPs that have deployed Arbor’s Peakflow SP product — collated and analyzed as part of Arbor’s ATLAS initiative — it appears that DDoS attacks are rising in number and volume as a result of the Israel-Hamas conflict. The graph below depicts the number of reported DDoS attacks initiated against Israel daily over the 1 June to 3 August period this year: Distributed Denial of Service (DDoS) attacks are used to flood a website or service with traffic to the point systems cannot cope, denying other users access to the website. Arbor detected a rise in the number of DDoS attacks targeting Israel in the first week of July, going from an average of 30 attacks per day to an average of 150 attacks initiated per day in July — peaking at 429 attacks on July 21st. Linking these cyberattacks to political situations, 30 June is when Israel publicly attributed the deaths of three kidnapped Israeli teenagers to Hamas, and on 7 July, “Operation Protective Edge” was launched by the country. As the political conflict raged on, so did the frequency of DDoS attacks until a drop occurred on 28 July lasting through 2 August. Arbor says the drop in attacks roughly correlates with cease fire talks which began 27 July. From 28 July through 2 August, there were 192 attacks recorded in total. On 3 August, the number of DDoS attacks rose sharply, with 268 attacks in total. In addition to the number of DDoS attacks over these time periods, the security researchers also noticed an increase in the peak size of these attacks. In the graph below, we can see that in June, no attacks exceeded 12Gbps. In July, seven DDoS attacks exceeded this size, with the largest peaking at 22.56Gbps on 12 July. When cease-fire talks fell apart on 3 August, the largest DDoS attack was recorded at a size of 29Gbps. The duration of DDoS attacks has also increased. In June, the average duration was 20 minutes — with a peak duration of 24 hours — and in July, the average duration was 1 hour 39 minutes. “As the intensity of the Israeli-Hamas conflict has increased, so has the number, size and duration of the DDoS attacks targeting Israel,” the researchers say. “Additionally, it even appears as if the attackers have made an effort to adhere to the “real world” calls for a cease-fire, resuming their attacks when the cease fire fell through.” Source: http://www.zdnet.com/israel-hamas-conflict-sparks-surge-in-ddos-attacks-7000032375/#ftag=RSS14dc6a9