Prolexic has issued a number of recommendations that organizations can use to validate their DDoS defenses, as well as protection services they receive from mitigation providers. Organizations sh…
See more here:
Tips for validating DDoS defenses

Prolexic has issued a number of recommendations that organizations can use to validate their DDoS defenses, as well as protection services they receive from mitigation providers. Organizations sh…
See more here:
Tips for validating DDoS defenses
The central organizer of a worldwide conspiracy to manipulate stock prices through a “botnet” network of virus-controlled computers was sentenced today to 71 months in prison and was ordered to pay a …
See the article here:
Fraudster who hired hackers to manipulate stock prices goes to prison
It seems as though just about anyone with Internet access can set up a profitable online enterprise these days — including a criminal one. And for one Illinois teen, YouTube and PayPal have been all too happy to help him make a fast (albeit illegal) buck. Brian Krebs has been sleuthing once again, and his target this time was a “stress testing” service called Asylum Stresser . Stress testing, of course, is the thin veil that skiddies (script kiddies) like to drape over a for-hire DDoS attack setup. According to Krebs and his cohorts, Asylum looks like it’s been built using fairly run-of-the-mill cybercrime kitware that’s promoted in underground forum sites. Its servers are based in Romania, and appear to be nestled safely in a data center that is nothing if not criminal-friendly. Nothing shocking so far, right? Anyone who has a few extra bucks (or BitCoins) to white label someone else’s criminal back-end can do this stuff. But here’s the twist: the kid Krebs believes is running Asylum Stesser is accepting PayPal payments and advertising on YouTube. Recently, Asylum’s user database was leaked to the web and it revealed that more than $35,000 had been sent to one chandlerdowns1995(at)gmail.com. Downs also appears to have hired an eager infomercial actor over on Fiverr. While the promo spot is good for a chuckle, it’s hard to believe that YouTube will jump all over a 30 second fan-made video for copyright infringement, but has somehow allowed an ad for an illegal DDoS service to be viewed more than 42,000 times. Downs maintains that it’s not his fault if people use the service to launch illegal attacks. Asylum Stresser was launched so that law-abiding folk can make sure their websites are resilient. Maybe that’s why PayPal and YouTube have been fine with ignoring what’s gone on to this point. Former U.S. Justice Department attorney Mark Rasch, however, feels differently. He told Krebs that if Downs triggers an attack after being paid to do so, he is “criminally and civilly liable.” Downs didn’t exactly made it difficult for Krebs to connect the dots here. Let’s see if PayPal and YouTube get their heads out of the sand now and do something before an Illinois court orders them to. For protection against your eCommerce site click here . Source: http://www.geek.com/news/paypal-turns-blind-eye-to-payments-totaling-35000-for-on-demand-ddos-1554902/
See the original post:
Paypal turns blind eye to payments totaling $35,000 for on-demand DDoS

 Two days before the May 13 elections, the Commission on Elections (Comelec) and the Philippine News Agency websites appeared inaccessible to the public. Cursory inspections of the websites of the Philippines’ Departments of Interior and Local Government, National Defense, Foreign Affairs, and Science and Technology, showed they were also apparently inaccessible. The pages for the Philippine National Police, the Army and Navy, and the Philippine Information Agency also could not be accessed. As of 4:10 pm., the Department of Science and Technology (DOST) acknowledged and confirmed distributed denial of service (DDoS) attacks occurring against government sites, but they did not mention where the attacks came from. In a text message to Rappler, Roy Espiritu of the DOST ICT Office said the attacks started on May 10 on gov.ph, then to additional gov.ph-based websites on May 11. He added that the DOST was working on neutralizing the attacks and determining the source. They are also assisting government agencies outside their secured servers who have asked for help. Interaksyon.com earlier reported on the possibility of the downtime being caused by a cyberattack, but noted that the Facebook page of Anonymous Philippines, a hacker-activist group, stated they would undertake no operations during this time. GMA wrote that its technical team “detected an overnight cyberattack that was still ongoing as of posting time on numerous Philippine websites, including GMA News Online, ABS-CBN News, Philippine Airlines, Globe, Smart, and more than two dozen Philippine government websites.” Based on referrer tags and forum activity, GMA also added the attacks seem to have come from Taiwan, linking to a Taiwanese webpage that seems to have reacted positively to the Philippine site downtime. The possibility of a cyberattack related to Philippine-Taiwanese tensions resulting from the shooting of a Taiwanese fisherman was also raised. While no announcement has been made by the Philippine government, Comelec spokesperson James Jimenez mentioned previously to Rappler that the Comelec website may have downtime due to the number of people visiting it, as well as the location of the Comelec website servers. It also repeated this in a recent tweet. As of 2:30 pm., Rappler could access the site, which appears to have had a redesign in time for the elections. With regard to election issues, those seeking information from the Comelec about finding one’s voting precinct but cannot access their homepage can contact the Comelec through the following hotlines: 525335; 5259297; 5259301; 5259302; 5259345; 5271892; 5516552; 5521451; 5523044. – Rappler.com For protection against your eCommerce site click here . Source: http://www.rappler.com/nation/28804-philippine-government-sites-inaccessible
Two days before the May 13 elections, the Commission on Elections (Comelec) and the Philippine News Agency websites appeared inaccessible to the public. Cursory inspections of the websites of the Philippines’ Departments of Interior and Local Government, National Defense, Foreign Affairs, and Science and Technology, showed they were also apparently inaccessible. The pages for the Philippine National Police, the Army and Navy, and the Philippine Information Agency also could not be accessed. As of 4:10 pm., the Department of Science and Technology (DOST) acknowledged and confirmed distributed denial of service (DDoS) attacks occurring against government sites, but they did not mention where the attacks came from. In a text message to Rappler, Roy Espiritu of the DOST ICT Office said the attacks started on May 10 on gov.ph, then to additional gov.ph-based websites on May 11. He added that the DOST was working on neutralizing the attacks and determining the source. They are also assisting government agencies outside their secured servers who have asked for help. Interaksyon.com earlier reported on the possibility of the downtime being caused by a cyberattack, but noted that the Facebook page of Anonymous Philippines, a hacker-activist group, stated they would undertake no operations during this time. GMA wrote that its technical team “detected an overnight cyberattack that was still ongoing as of posting time on numerous Philippine websites, including GMA News Online, ABS-CBN News, Philippine Airlines, Globe, Smart, and more than two dozen Philippine government websites.” Based on referrer tags and forum activity, GMA also added the attacks seem to have come from Taiwan, linking to a Taiwanese webpage that seems to have reacted positively to the Philippine site downtime. The possibility of a cyberattack related to Philippine-Taiwanese tensions resulting from the shooting of a Taiwanese fisherman was also raised. While no announcement has been made by the Philippine government, Comelec spokesperson James Jimenez mentioned previously to Rappler that the Comelec website may have downtime due to the number of people visiting it, as well as the location of the Comelec website servers. It also repeated this in a recent tweet. As of 2:30 pm., Rappler could access the site, which appears to have had a redesign in time for the elections. With regard to election issues, those seeking information from the Comelec about finding one’s voting precinct but cannot access their homepage can contact the Comelec through the following hotlines: 525335; 5259297; 5259301; 5259302; 5259345; 5271892; 5516552; 5521451; 5523044. – Rappler.com For protection against your eCommerce site click here . Source: http://www.rappler.com/nation/28804-philippine-government-sites-inaccessible
View original post here:
9 PH gov’t sites inaccessible due to DDoS Attack
ReputationChanger.com was the most recent target in a string of high-profile cyber-attacks against U.S. web companies and governmental organizations. Reputation.com, LivingSocial and Name.com have all announced recently that they have been the targets of successful attacks by hackers. Tens of millions of consumers have been asked to change passwords in the wake of these attacks with large numbers of the population informed that personal data may have been accessed. A hack of the Associated Press account in Twitter resulted in a temporary loss on U.S. stock markets of $200 billion in late April. The U.S. Defense Department accused Chinese government-backed hackers this week of a sustained cyber campaign which successfully targeted governmental and defense contractor websites. The Chinese later denied these allegations. ReputationChanger.com was indeed targeted by an attack from a Chinese IP address that lasted most of the day. While the company’s public website was taken down for roughly half an hour in a distributed denial of service attack (DDoS), an investigation confirms that the company’s critical information — including client data — remained untouched. “The attack brought down our main website briefly but I think overall it revealed the strength and security of our operation in a way that we are truly proud of,” comments the company’s president, Michael Zammuto. “Because of the system set up, no client data was in danger of being accessed or compromised — and indeed, no client data was accessed or compromised. No action is required of any client although periodic password changes are always recommended.” Even a cyber-attack targeting the company’s Command Center, the firm’s online reputation management platform, could not have led to illicit data access. “The confidentiality of what we do is critical, and we are endlessly devoted to maintaining the complete privacy of our clients,” Zammuto offers. “As such, we have a highly distributed cloud system, response teams and processes in place to prepare for cyber threats.” Though the identity of the cyber assailant is yet unknown, Zammuto says the impetus for the attack is likely the high-profile client list that ReputationChanger.com maintains. “We were surely targeted because of the very important clients that we work with,” he affirms. ReputationChanger.com’s clientele encompasses governments, political figures, educational institutions, celebrities, and major, internationally-recognized businesses and brands. Despite the brief downtime experienced on the ReputationChanger.com website, Zammuto says that he is ultimately thrilled with how well the enterprise held up in the face of a malicious online assault. “I am very pleased with the performance of our network security team and partners,” he remarks. “It is a great reminder of how valuable investments are in these areas. They kept us safe from a vicious online enemy. It is because of their hard work and their expertise that ReputationChanger.com’s clients can rest assured that their confidential data is in the best possible hands.” ReputationChanger.com is the top rated online reputation management firm according to Top SEOs and was announced as a finalist for the Red Herring 100 earlier this week Both organizations citing the firm’s technology and its commitment to serving its clients. For protection against your eCommerce site click here . Source: http://online.wsj.com/article/PR-CO-20130509-912785.html?mod=googlenews_wsj
Visit link:
Nationwide DDoS Attack Hits ReputationChanger.com
Sven Olaf Kamphuis, owner and manager of Dutch “bulletproof hosting” firm Cyberbunker and of CB3ROB ISP, has been extradited to the Netherlands on Monday. The 35-year-old Dutch citizen was arrested…
Taken from:
Spamhaus DDoS suspect extradited to his home country
The German Anti-Botnet Advisory Centre is warning (in German) users about a new ransomware / BKA Trojan variant that accuses users of being involved in the reproduction of pornographic material involv…
The German Anti-Botnet Advisory Centre is warning (in German) users about a new ransomware / BKA Trojan variant that accuses users of being involved in the reproduction of pornographic material involv…
The hacktivist collective Anonymous, along with other hacker groups based in the Middle East and North Africa, began an operation, dubbed “OpUSA,” targeting the websites of nine major U.S. government agencies and over 130 banks earlier this morning in a protest against American foreign policy. Targets include the Pentagon, the National Security Agency, the FBI and the White House, along with the websites of banks such as Bank of America, Capital One and TD Bank. Calling themselves the “N4m3le55 Cr3w,” the collective of hacker groups said in a statement that it aims to make sure “this May 7th will be a day to remember.” The relatively amorphous Anonymous, a decentralized and loosely associated collective of hackers, grew out of the internet imageboard 4Chan back in the early 2000s. As the very interesting and informative 2012 documentary on the group, “We Are Legion: The Story of the Hacktivists,” highlights, there is no one group called Anonymous with one set of goals or ideals. Rather there are a collection of groups and individuals that operate under the name Anonymous, often with varying agendas ranging from principle social activism to just messing with people because they can. Because of this, their actions can range from the awesome (such as their support for protesters during the Arab uprisings) to the simply mean and unnecessary (such as posting flashing animations on the website of an epilepsy support group). Anonymous is joined by groups including the Izz al-Din Qassam Cyber Fighters, whose sole aim is apparently to get the “Innocence of Muslims” video removed from YouTube. Other groups involved in OpUSA include Mauritania hackers, Muslim liberation army, antisec, and lulzsec. Over the past six months, the Qassam Cyber Fighters have successfully carried out distributed denial of service (DDoS) attacks against large American banks. The groups have been publicizing their planned operation for weeks now, and in their statement posted on the website Pastebin on April 21 they said that America will pay for the war crimes it has committed: “America you have committed multiple war crimes in Iraq, Afghanistan, Pakistan, and recently you have committed war crimes in your own country. You have killed hundreds of innocent children and families with drones, guns, and now bombs. America you have hit thousands of people where it hurts them, now it is our time for our Lulz. For this you shall pay.” For protection against your eCommerce site click here . Source: http://current.com/technology/94112350_anonymous-opusa-massive-cyber-attack-planned-for-wednesday-against-government-and-banks.htm
Read More:
Anonymous OpUSA: Massive Cyber Attack Planned For Wednesday May 8 Against Government and Banks

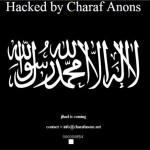 Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx
Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx
See more here:
May 7 2013 – OpUSA hacking spree kicks off early