A recent expose shines a light onto the strange world of “booter” or “stressor” web sites which offer DDoS-attacks-for-hire Is an online payment giant Paypal unwittingly enabling DDoS attacks? That’s the question posed by security researchers who have studied a small, weird corner of the market for distributed denial of service (DDoS) services: so-called “booter” or “stressor” web sites. Speaking at The Security B-Sides Boston security conference on Saturday, independent researchers Allison Nixon and Brandon Levene said that their investigation of booter sites found that many rely on legitimate online services, including Paypal to accept payment on behalf of customers interested in attacking web sites they do not own, and Cloudflare, a DDoS prevention service. The presentation was just the latest to peek into the strange world of “booter” or “stressor” web sites, which offer DDoS attacks for hire, often targeted at online gaming services popular with teenagers. In the past week, the web site krebsonsecurity.com published exposes on two such sites: assylumstressor.net and Ragebooter.net, both booter services for hire. In the process, Krebs revealed the identities of the purported owners of the sites and details of conversations he had with them about their services. In their presentation Saturday, Levene and Nixon, who assisted Krebs in his research, said that the booter sites were common online, but wholly different from the massive, 300Gbps attacks directed at Spamhaus, or the site-crippling DDoS attacks on leading banks and financial services firms like Citi, Chase, Wells Fargo and others in recent months. Rather, the services use mostly simple, reflected DNS and UDP flood attacks to knock small sites and residential home routers offline, the two researchers said. Many of the features of sites like Ragebooter.net are poorly designed or don’t work at all, said Nixon. Most victims are very often small websites hosting online gaming servers. In fact, the most reliable customers of booter sites are often other booter sites, said Nixon. The sites are not hugely profitable, but do generate some income. An analysis of data on the site Asylumstressor.com by Nixon and Levene suggest that site operators made, at most, $23,000 in 2012 – though probably much less. The sites operate more or less in the open. Speaking with Brian Krebs last week, a Tennessee man named Justin Poland, the operator of ragebooter.net, argued that the services were legal. “Since it is a public service on a public connection to other public servers this is not illegal,” Poland told Krebs in a Facebook chat. Poland even claimed to be working on behalf of the local FBI, turning over information gleaned from his service to law enforcement as needed. The Memphis FBI would not confirm or deny that Poland’s claims were true. Legal or not, most booter sites operate more or less in the open and with impunity, Nixon told an audience at B-Sides Boston, which was held at Microsoft’s New England Research and Development Center (NERD) in Cambridge. Site operators – many teenagers and 20-somethings with little technical sophistication – make little effort to conceal their identities. Paypal payments are often sent to e-mail accounts that are also associated with public Facebook profiles, making it easy to link booter sites to real world identities like Poland’s, she said. Law enforcement seems unconcerned with small scale attack sites like Ragebooter.net, or those who operate them, meaning that booter site operators continue to operate despite ample evidence about who they are and the illegal nature of their business, Nixon said. Similarly, services like PayPal and Cloudflare enable small-scale DDoS operations to continue, by turning a blind eye to the true nature of their businesses. Nixon said as many as 70 percent of booter sites use Cloudflare, a DDoS protection site. The service mainly protects booter sites from other booter sites, she said. Paypal isn’t the only online payment service, but it is easy and convenient to use and widely respected. Inexperienced booters who had to go through the trouble of setting up an account at a site like LibertyReserve might think twice, Nixon argued. In an e-mail statement to ITworld and other news outlets, Paypal said that it couldn’t discuss the specifics of customer accounts but that it “will review suspicious accounts for malicious activity and work with law enforcement to ensure cyber criminals are reported properly.” “We take security very seriously at PayPal,” the statement continued. “We do not condone the use of our site in the sale or dissemination of tools, which have the sole purpose to attack customers and illegally take down web sites.” Cloudflare CEO Matthew Prince said that his company protects millions of web sites – most of them legitimate private and public sector entities. However, his company doesn’t discriminate, and Prince admits that some sites protected by Cloudflare are troubling, including the booter and stressor sites. Cloudflare works closely with law enforcement and always responds promptly to requests for information from the courts or law enforcement offiicals. However, in the absence of any action by law enforcement, Prince said that it isn’t for him or his company to decide who to work with. “I do find it troubling when there are extralegal measures taken to determine what is and is not going on,” he said, in an apparent reference to the investigation by Krebs, Nixon and Levene. “How far do you go with that, if someone assumes XYZ shouldn’t be on the Internet? Should Google remove them from their search index?” he asked. “We believe in due process,” said Prince. Source: http://www.itworld.com/it-management/357306/legitimate-online-services-enabling-ddos-attacks-hire-sites
Read this article:
Legitimate online services enable DDoS-attacks-for-hire sites


 Two days before the May 13 elections, the Commission on Elections (Comelec) and the Philippine News Agency websites appeared inaccessible to the public. Cursory inspections of the websites of the Philippines’ Departments of Interior and Local Government, National Defense, Foreign Affairs, and Science and Technology, showed they were also apparently inaccessible. The pages for the Philippine National Police, the Army and Navy, and the Philippine Information Agency also could not be accessed. As of 4:10 pm., the Department of Science and Technology (DOST) acknowledged and confirmed distributed denial of service (DDoS) attacks occurring against government sites, but they did not mention where the attacks came from. In a text message to Rappler, Roy Espiritu of the DOST ICT Office said the attacks started on May 10 on gov.ph, then to additional gov.ph-based websites on May 11. He added that the DOST was working on neutralizing the attacks and determining the source. They are also assisting government agencies outside their secured servers who have asked for help. Interaksyon.com earlier reported on the possibility of the downtime being caused by a cyberattack, but noted that the Facebook page of Anonymous Philippines, a hacker-activist group, stated they would undertake no operations during this time. GMA wrote that its technical team “detected an overnight cyberattack that was still ongoing as of posting time on numerous Philippine websites, including GMA News Online, ABS-CBN News, Philippine Airlines, Globe, Smart, and more than two dozen Philippine government websites.” Based on referrer tags and forum activity, GMA also added the attacks seem to have come from Taiwan, linking to a Taiwanese webpage that seems to have reacted positively to the Philippine site downtime. The possibility of a cyberattack related to Philippine-Taiwanese tensions resulting from the shooting of a Taiwanese fisherman was also raised. While no announcement has been made by the Philippine government, Comelec spokesperson James Jimenez mentioned previously to Rappler that the Comelec website may have downtime due to the number of people visiting it, as well as the location of the Comelec website servers. It also repeated this in a recent tweet. As of 2:30 pm., Rappler could access the site, which appears to have had a redesign in time for the elections. With regard to election issues, those seeking information from the Comelec about finding one’s voting precinct but cannot access their homepage can contact the Comelec through the following hotlines: 525335; 5259297; 5259301; 5259302; 5259345; 5271892; 5516552; 5521451; 5523044. – Rappler.com For protection against your eCommerce site click here . Source: http://www.rappler.com/nation/28804-philippine-government-sites-inaccessible
Two days before the May 13 elections, the Commission on Elections (Comelec) and the Philippine News Agency websites appeared inaccessible to the public. Cursory inspections of the websites of the Philippines’ Departments of Interior and Local Government, National Defense, Foreign Affairs, and Science and Technology, showed they were also apparently inaccessible. The pages for the Philippine National Police, the Army and Navy, and the Philippine Information Agency also could not be accessed. As of 4:10 pm., the Department of Science and Technology (DOST) acknowledged and confirmed distributed denial of service (DDoS) attacks occurring against government sites, but they did not mention where the attacks came from. In a text message to Rappler, Roy Espiritu of the DOST ICT Office said the attacks started on May 10 on gov.ph, then to additional gov.ph-based websites on May 11. He added that the DOST was working on neutralizing the attacks and determining the source. They are also assisting government agencies outside their secured servers who have asked for help. Interaksyon.com earlier reported on the possibility of the downtime being caused by a cyberattack, but noted that the Facebook page of Anonymous Philippines, a hacker-activist group, stated they would undertake no operations during this time. GMA wrote that its technical team “detected an overnight cyberattack that was still ongoing as of posting time on numerous Philippine websites, including GMA News Online, ABS-CBN News, Philippine Airlines, Globe, Smart, and more than two dozen Philippine government websites.” Based on referrer tags and forum activity, GMA also added the attacks seem to have come from Taiwan, linking to a Taiwanese webpage that seems to have reacted positively to the Philippine site downtime. The possibility of a cyberattack related to Philippine-Taiwanese tensions resulting from the shooting of a Taiwanese fisherman was also raised. While no announcement has been made by the Philippine government, Comelec spokesperson James Jimenez mentioned previously to Rappler that the Comelec website may have downtime due to the number of people visiting it, as well as the location of the Comelec website servers. It also repeated this in a recent tweet. As of 2:30 pm., Rappler could access the site, which appears to have had a redesign in time for the elections. With regard to election issues, those seeking information from the Comelec about finding one’s voting precinct but cannot access their homepage can contact the Comelec through the following hotlines: 525335; 5259297; 5259301; 5259302; 5259345; 5271892; 5516552; 5521451; 5523044. – Rappler.com For protection against your eCommerce site click here . Source: http://www.rappler.com/nation/28804-philippine-government-sites-inaccessible 
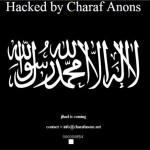 Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx
Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx