Iranian hackers launched attacks as part of a campaign against the country’s oil and gas industry, according to current and former U.S. government officials. Iranian hackers have amped up a campaign of cyber-attacks against America’s energy industry, according to a report from The Wall Street Journal . Citing current and former U.S. officials speaking under the blanket of anonymity, the Journal reported that Iranian hackers accessed control system software that could have allowed them to manipulate oil or gas pipelines. The attacks raise the stakes in cyber-space between the U.S. and Iran, which has been accused by U.S. officials of being behind a spate of distributed denial-of-service attacks (DDoS) against U.S. banks stretching back to 2012. “This is representative of stepped-up cyber activity by the Iranian regime. The more they do this, the more our concerns grow,” a source told the Journal . “What they have done so far has certainly been noticed, and they should be cautious.” Alireza Miryousefi, Iran’s spokesperson at the United Nations, denied any connection between hackers and the regime in an interview with the Journal . The officials who spoke to The Wall Street Journal did not name any of the energy companies targeted in the attacks. But two former officials said oil and gas companies located along the Canadian border were among those hit. Word of the attacks comes a week after Charles Edwards, deputy inspector general at the U.S. Department of Homeland Security, told members of a Senate subcommittee that industrial control systems were increasingly coming under attack in cyber-space in ways that could potentially cause “large-scale power outages or man-made environmental disasters.” Securing these systems is complicated, as many are more interconnected with the Internet than people realize, explained Tom Cross, director of security research at network security vendor Lancope. “It is also difficult to fix security flaws with these systems because they aren’t designed to be patched and restarted frequently,” he said. “It is extremely important,” he continued, “that operators of industrial control networks monitor those networks with systems that can identify anomalous activity that might be associated with an attack. Because of the relatively homogenous nature of network activity on many control systems networks, anomaly detection can be can be a powerful tool in an environment where other kinds of security approaches fall flat.” Much of the talk about improving the security of critical infrastructure companies has focused on information sharing between the government and private sector. Improving communication between government and business figured prominently in the executive order on cyber-security that President Barack Obama issued in February. However, many officials and security experts have said that the order does not undo the need for legislation. “The increases in cyber-assaults on our energy systems from Iranian-backed hackers are another signal to the government and the industry that measures must be taken to fortify the security of our critical infrastructure,” said Lila Kee, chief product and marketing officer at GlobalSign and a North American Energy Standards Board (NAESB) board member. “However, there is a fine line between cyber-security regulation and voluntary standards,” she said. “Regulations cannot be so rigid so as to prevent protection from today’s evolving advanced persistent threats, and voluntary standards cannot be so loose so as to provide no purpose. In today’s modern world of malware, solutions must be fluid and scalable to battle aggressive cyber-attacks.” Source: http://www.eweek.com/security/iranian-hackers-launching-cyber-attacks-on-us-energy-firms-report/
Read More:
Iranian Hackers Launching Cyber-Attacks on U.S. Energy Firms: Report


 Two days before the May 13 elections, the Commission on Elections (Comelec) and the Philippine News Agency websites appeared inaccessible to the public. Cursory inspections of the websites of the Philippines’ Departments of Interior and Local Government, National Defense, Foreign Affairs, and Science and Technology, showed they were also apparently inaccessible. The pages for the Philippine National Police, the Army and Navy, and the Philippine Information Agency also could not be accessed. As of 4:10 pm., the Department of Science and Technology (DOST) acknowledged and confirmed distributed denial of service (DDoS) attacks occurring against government sites, but they did not mention where the attacks came from. In a text message to Rappler, Roy Espiritu of the DOST ICT Office said the attacks started on May 10 on gov.ph, then to additional gov.ph-based websites on May 11. He added that the DOST was working on neutralizing the attacks and determining the source. They are also assisting government agencies outside their secured servers who have asked for help. Interaksyon.com earlier reported on the possibility of the downtime being caused by a cyberattack, but noted that the Facebook page of Anonymous Philippines, a hacker-activist group, stated they would undertake no operations during this time. GMA wrote that its technical team “detected an overnight cyberattack that was still ongoing as of posting time on numerous Philippine websites, including GMA News Online, ABS-CBN News, Philippine Airlines, Globe, Smart, and more than two dozen Philippine government websites.” Based on referrer tags and forum activity, GMA also added the attacks seem to have come from Taiwan, linking to a Taiwanese webpage that seems to have reacted positively to the Philippine site downtime. The possibility of a cyberattack related to Philippine-Taiwanese tensions resulting from the shooting of a Taiwanese fisherman was also raised. While no announcement has been made by the Philippine government, Comelec spokesperson James Jimenez mentioned previously to Rappler that the Comelec website may have downtime due to the number of people visiting it, as well as the location of the Comelec website servers. It also repeated this in a recent tweet. As of 2:30 pm., Rappler could access the site, which appears to have had a redesign in time for the elections. With regard to election issues, those seeking information from the Comelec about finding one’s voting precinct but cannot access their homepage can contact the Comelec through the following hotlines: 525335; 5259297; 5259301; 5259302; 5259345; 5271892; 5516552; 5521451; 5523044. – Rappler.com For protection against your eCommerce site click here . Source: http://www.rappler.com/nation/28804-philippine-government-sites-inaccessible
Two days before the May 13 elections, the Commission on Elections (Comelec) and the Philippine News Agency websites appeared inaccessible to the public. Cursory inspections of the websites of the Philippines’ Departments of Interior and Local Government, National Defense, Foreign Affairs, and Science and Technology, showed they were also apparently inaccessible. The pages for the Philippine National Police, the Army and Navy, and the Philippine Information Agency also could not be accessed. As of 4:10 pm., the Department of Science and Technology (DOST) acknowledged and confirmed distributed denial of service (DDoS) attacks occurring against government sites, but they did not mention where the attacks came from. In a text message to Rappler, Roy Espiritu of the DOST ICT Office said the attacks started on May 10 on gov.ph, then to additional gov.ph-based websites on May 11. He added that the DOST was working on neutralizing the attacks and determining the source. They are also assisting government agencies outside their secured servers who have asked for help. Interaksyon.com earlier reported on the possibility of the downtime being caused by a cyberattack, but noted that the Facebook page of Anonymous Philippines, a hacker-activist group, stated they would undertake no operations during this time. GMA wrote that its technical team “detected an overnight cyberattack that was still ongoing as of posting time on numerous Philippine websites, including GMA News Online, ABS-CBN News, Philippine Airlines, Globe, Smart, and more than two dozen Philippine government websites.” Based on referrer tags and forum activity, GMA also added the attacks seem to have come from Taiwan, linking to a Taiwanese webpage that seems to have reacted positively to the Philippine site downtime. The possibility of a cyberattack related to Philippine-Taiwanese tensions resulting from the shooting of a Taiwanese fisherman was also raised. While no announcement has been made by the Philippine government, Comelec spokesperson James Jimenez mentioned previously to Rappler that the Comelec website may have downtime due to the number of people visiting it, as well as the location of the Comelec website servers. It also repeated this in a recent tweet. As of 2:30 pm., Rappler could access the site, which appears to have had a redesign in time for the elections. With regard to election issues, those seeking information from the Comelec about finding one’s voting precinct but cannot access their homepage can contact the Comelec through the following hotlines: 525335; 5259297; 5259301; 5259302; 5259345; 5271892; 5516552; 5521451; 5523044. – Rappler.com For protection against your eCommerce site click here . Source: http://www.rappler.com/nation/28804-philippine-government-sites-inaccessible 
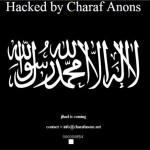 Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx
Islamist element in attacks. A pro-Islamic, anti-American hacking campaign appears to have jumped the gun and started early with hundreds of sites being compromised today. Set to take place on May 7 this month – thought to be US time – and targeting government sites in the US, Israel and India, the campaign is called #OpUSA. It is coordinated mainly through Twitter and postings on sites like Pastebin, with an unknown amount of participants. However, lists of compromised sites are already apppearing, with a group called “X-Blackerz Inc” claiming to have hacked “100 US websites”, posting anti-American messages. iTnews loaded some of the sites listed which have India-related domain names, and found them defaced. Elswhere, a group calling itself Charaf Anons posted a list of 73 defaced sites on Pastebin. The website of the Honolulu, Hawaii Police Department was also claimed to be hacked, but as of writing, it is not defaced and operates normally. However, the hackers say they have captured databases that include the Honolulu Police Department staff logins and passwords. Another one was also posted with names and phone numbers that iTnews was able to verify as belonging to police officers in Honolulu. There is more to come: on May 7, the hackers are threatening to release a trove of “all governments emails of USA” [sic] captured by them. From the Anonghost Twitter account Security researcher Analysis Intelligence believes OpUSA features “self-proclaimed online freedom fighters” such as the Pakistani ZCompany Hacking Crew and Palestinians Izz ad-Din al-Qassam Cyber Fighters. These and other groups have hacked thousands of websites in the past, leaked credit card information for American and Israeli individuals and launched denial of service attacks against US banks, according to Analysis Intelligence. The motive for the OpUSA attacks are political, seeking revenge against drone attacks and military action in Iraq, Afghanistan, Gaza and Pakistan, the analysts believe. For DDoS protection click here . Source: http://www.itnews.com.au/News/342192,opusa-hacking-spree-kicks-off-early.aspx